ASP.NET Core Authorization Strategies: RBAC vs. ABAC vs. Policy-Based — Enterprise Decision Guide
Authorization is the last line of defense in enterprise APIs, and most teams get it wrong — not because they choose the wrong technology, but because they choose the wrong model for their context.
Want implementation-ready .NET source code you can adapt fast? Join Coding Droplets on Patreon. 👉 https://www.patreon.com/CodingDroplets
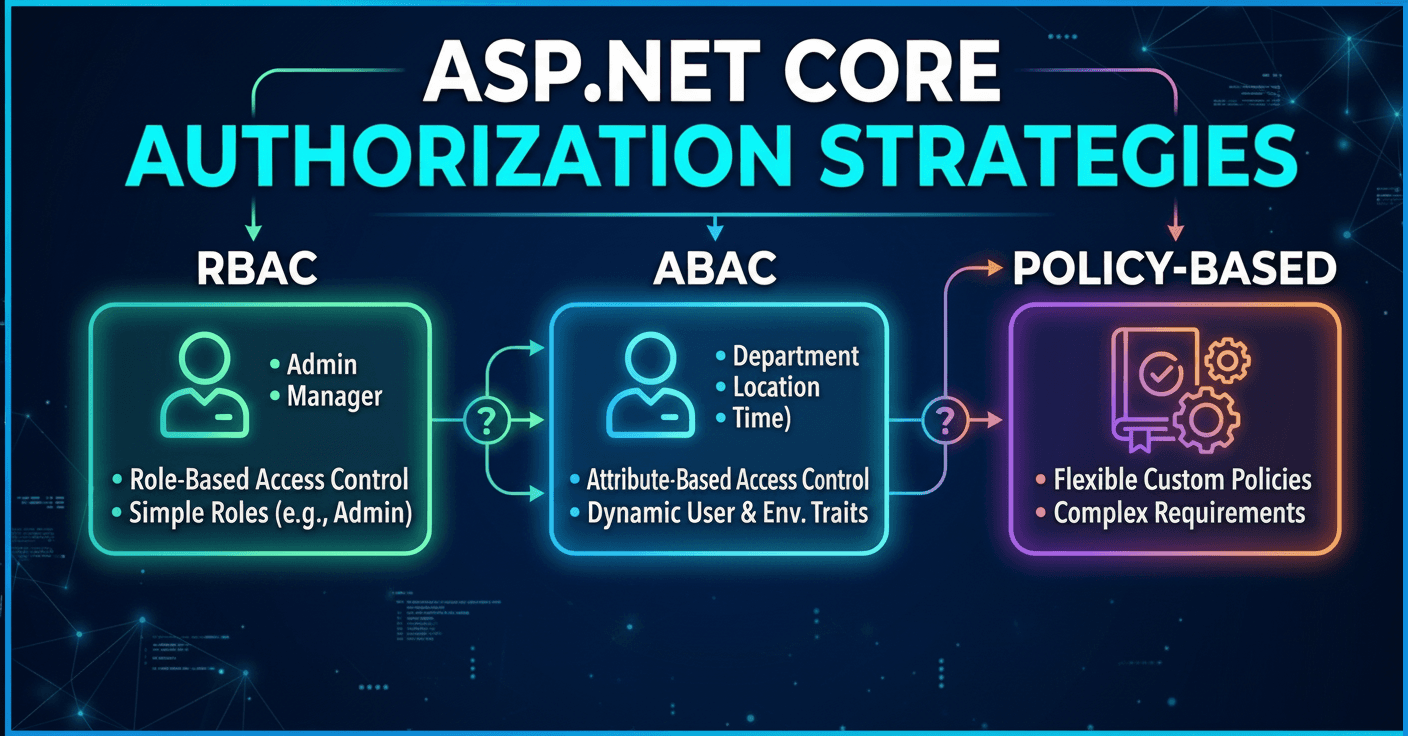
ASP.NET Core ships with three distinct authorization models that enterprise teams tend to blend together without a clear architectural rationale: role-based authorization, claims-based authorization through policies, and resource-based authorization. Each model serves a different decision surface. Using the wrong one at the wrong layer creates authorization logic scattered across controllers, handlers, and services — logic that is hard to audit, harder to change, and nearly impossible to test confidently.
This article frames the decision in terms enterprise architects and senior engineers actually face: what scope of access control problem are you solving, who owns the rules, and how often do those rules change?
Why Authorization Model Selection Matters at Scale
Authorization is not a feature. It is infrastructure. Teams that treat it as a feature bolt it on incrementally — role checks here, policy checks there, a service-level guard buried in a domain method — and end up with authorization logic that no single developer can reason about holistically.
Enterprise systems face authorization pressure from three directions simultaneously. Compliance teams demand auditable, centralized access rules. Product teams want flexible, context-sensitive permissions that respond to subscription levels or organizational hierarchy. Platform teams need authorization that composes cleanly across microservices without becoming a distributed mess of shared constants.
Selecting the right model upfront is how you avoid building authorization from scratch three times before the system goes to production.
The Three Models: A Structural Overview
ASP.NET Core's authorization infrastructure is layered, and the three models sit at different levels of that layer cake.
Role-Based Authorization (RBAC) is the oldest model and the one most teams reach for first. It answers the question: what role does this user hold in the system? Roles are coarse-grained identities — Admin, Manager, Editor, Viewer. Role checks live in attributes or middleware and evaluate quickly because they require no external lookup. The limitation is that roles are static. They do not encode context. A Manager role does not tell the authorization system whether this manager is authorized to approve expenses for this specific department, at this specific amount, under this specific approval workflow.
Policy-Based Authorization is ASP.NET Core's native answer to fine-grained, composable access rules. Policies are named requirements registered in DI, evaluated by handlers. They solve the "roles are not enough" problem by allowing arbitrary logic: minimum age checks, subscription tier checks, department membership, feature flag gates. Policies evaluate against the authenticated user's claims and optionally against a resource. They are testable in isolation because handlers are plain classes. The tradeoff is indirection — understanding what access rule applies to a given endpoint requires tracing from attribute to policy name to handler registration.
Resource-Based Authorization extends the policy model to answer: does this user have access to this specific resource instance? It involves calling IAuthorizationService.AuthorizeAsync explicitly inside controller actions or domain services, passing both the policy name and the resource object. This is the model you need when the authorization decision depends on data — the resource's owner, its status, its organizational unit, or its relationship to the requesting user. Resource-based authorization cannot be expressed purely in middleware because the resource data must be loaded first.
The Enterprise Decision Framework
The right model is determined by answering three questions about each authorization requirement.
Question 1: Who defines and owns the access rule?
If access rules are defined by system architects at design time and rarely change — you are dealing with structural authorization. Role-based or simple policy-based authorization fits. If access rules are defined by business administrators at runtime — who can approve what amounts, which team leads can view which projects — you are dealing with dynamic authorization. You need policies backed by data stores, not hardcoded handler logic.
Question 2: Does the access decision depend on the resource's data?
If the answer is yes in any form — even "only for premium subscribers viewing their own data" — you need resource-based authorization. Attempting to encode resource-instance rules into role checks or static policies leads directly to leaky abstractions that require application code to pre-filter results before returning them.
Question 3: How granular does the permission model need to be?
A three-tier SaaS with Admin, User, and ReadOnly roles can sustain RBAC through its entire product lifecycle. An enterprise platform managing multi-departmental data with delegated access, approval chains, and tenant-scoped permissions cannot. The inflection point is when the number of roles needed to express all access rules approaches the number of users — that is a signal the model has broken down.
RBAC: Where It Holds and Where It Breaks
Role-based authorization holds well in systems with stable organizational hierarchy, clear role boundaries, and authorization requirements that do not depend on data values. Internal tooling, admin portals with three or four distinct access levels, and simple SaaS tiers are RBAC territory.
RBAC breaks in systems that need to express delegation (this user is acting on behalf of), ownership (this user can only modify records they created), or condition-scoped access (this user can approve requests under $10,000). Each of these requires data — and RBAC has no natural place for data.
The organizational pressure that kills RBAC at scale is role explosion. Teams attempt to encode context into role names — RegionalManager_NorthAmerica, FinanceApprover_Level2 — until the role list becomes unmaintainable and the cognitive overhead of granting access exceeds the overhead of building a proper permission model.
Policy-Based Authorization: The Versatile Middle Ground
Policy-based authorization is the right default for enterprise systems. It is expressive enough to capture most requirements, testable in isolation, and extensible when needs grow.
The key architectural discipline is treating policy names as contracts, not implementation details. Policy names like CanApproveExpenseReports or RequiresActiveSubscription communicate intent. Policy names like Policy_v3_AdminOrManagerOrDelegate communicate that the policy layer has been used as a scratchpad.
Policies compose. A single endpoint can require multiple policies, each satisfied independently. Requirements within a policy can be combined. This composability is the feature that makes policy-based authorization scale without collapsing into a maze of conditional logic.
The failure mode to avoid is handler bloat — authorization handlers that query databases, call external services, and perform domain logic. Handlers should evaluate requirements against claims already present in the principal, or against the resource passed to the authorize call. Heavy data access in handlers creates subtle coupling between authorization and domain logic that makes both harder to test and evolve.
ABAC and Resource-Based Authorization: When Data Drives Decisions
Attribute-Based Access Control (ABAC) is the formal model where authorization decisions are computed from attributes of the subject (the user), the resource, and the environment (time, location, request context). ASP.NET Core's resource-based authorization is the practical implementation path for ABAC within the framework.
Enterprise scenarios that require ABAC include: multi-tenant platforms where tenants configure their own access policies, regulated environments where access is time-bounded or location-bounded, and systems with ownership semantics where creators have elevated rights over their own records.
The critical discipline for resource-based authorization is ensuring it runs after data retrieval, not as a gate that prevents retrieval. The pattern is: load the resource, authorize against it, return the result or 403. Teams that attempt to pre-filter at the query level — building authorization rules into EF Core query filters — create implicit coupling that makes authorization invisible and audit trails incomplete.
Composition Patterns for Complex Systems
Enterprise systems rarely require a single authorization model exclusively. The practical architecture layers them:
Structural access — can this user access this module at all — is handled through middleware-level policy enforcement, evaluated before the request reaches the controller. This is RBAC or simple policy territory.
Feature-level access — can this user perform this action — is handled through controller-level policy attributes. This is policy-based authorization territory.
Resource-level access — can this user perform this action on this specific record — is handled through explicit IAuthorizationService calls inside controller actions or application service methods after the resource is loaded. This is resource-based authorization territory.
This layered approach keeps each authorization concern at the appropriate layer of the stack. Structural rules live in registration code. Feature rules live in attributes. Resource rules live in application logic where the resource exists.
Authorization and Audit: The Enterprise Non-Negotiable
Any enterprise authorization architecture must produce an auditable trail. Which authorization decisions were made, on behalf of which user, for which resource, at what time, with what outcome.
ASP.NET Core's authorization infrastructure does not produce this trail automatically. Teams must instrument it — through authorization handler logging, through application event recording, or through structured audit logging in the resource-level authorization path.
The architectural discipline is deciding where this audit responsibility lives before the first handler is written. Retrofitting audit logging into an authorization architecture built without it is significantly more painful than designing for it from the start.
The Migration Problem: Evolving From RBAC to Policy-Based
Most enterprise teams inherit RBAC systems and need to evolve them without a big-bang migration. The practical migration path is additive: introduce policies that wrap existing role checks, then gradually refine those policies to encode richer requirements as business needs demand.
The mistake to avoid is running both models in parallel indefinitely — some endpoints checking roles, others checking policies, with no consistent mental model for which pattern applies where. Inconsistency in authorization models is an audit finding waiting to happen.
Frequently Asked Questions
Is RBAC obsolete for enterprise .NET applications? No. RBAC remains the right model for systems where access control maps cleanly to organizational structure and roles remain stable. It becomes insufficient when access decisions require data attributes that roles cannot encode. Many enterprise systems use RBAC at the structural level and policy-based or resource-based authorization for feature and data-level decisions.
Can ASP.NET Core's policy system implement ABAC natively?
Yes, through resource-based authorization. When you pass the resource object to IAuthorizationService.AuthorizeAsync, your handlers have access to both user claims and resource attributes, which is the ABAC decision surface. The framework does not label it ABAC, but the capability is present.
Should authorization handlers query the database? Sparingly. Authorization handlers that perform heavy data access introduce latency on every authorized request and create coupling between the authorization layer and data access patterns. Prefer enriching the user's claims at login time with attributes needed for authorization, and design handlers to evaluate against those claims. Reserve database access in handlers for fine-grained resource-instance checks where the resource attribute cannot be known at login time.
How should authorization be handled in ASP.NET Core microservices? Each service should enforce its own authorization independently, using the same token claims as the authorization source. Shared authorization libraries that enforce rules across services are a maintenance liability — they create coupling that makes services harder to deploy independently. Centralize authorization policy definitions in a shared library if you must share constants, but keep handler execution local to each service.
What is the right way to test authorization policies?
Authorization handlers are plain classes and can be tested with standard unit tests by constructing the AuthorizationHandlerContext directly with controlled claims and resources. Integration tests should verify that protected endpoints return the correct HTTP status codes for authenticated users with different permission configurations, not that specific handler logic is invoked.
How do permission-based systems differ from policy-based systems in ASP.NET Core? Permission-based systems typically represent fine-grained actions as discrete string values — "invoices.approve", "users.delete" — stored as claims and evaluated in policies. This is a refinement of policy-based authorization, not a separate model. The advantage is that permissions are data-driven and can be managed at runtime without code changes. The tradeoff is that permission proliferation requires careful governance to avoid the same explosion problem that kills RBAC.
When should resource-based authorization run in a request pipeline? After the resource has been loaded from the data store, inside the controller action or application service method. Never before — you cannot authorize access to a resource you have not yet retrieved, and attempting to do so pushes authorization logic into query layers where it is invisible to reviewers and auditors.