Duende IdentityServer vs Keycloak vs OpenIddict in .NET: Which to Use in 2026?
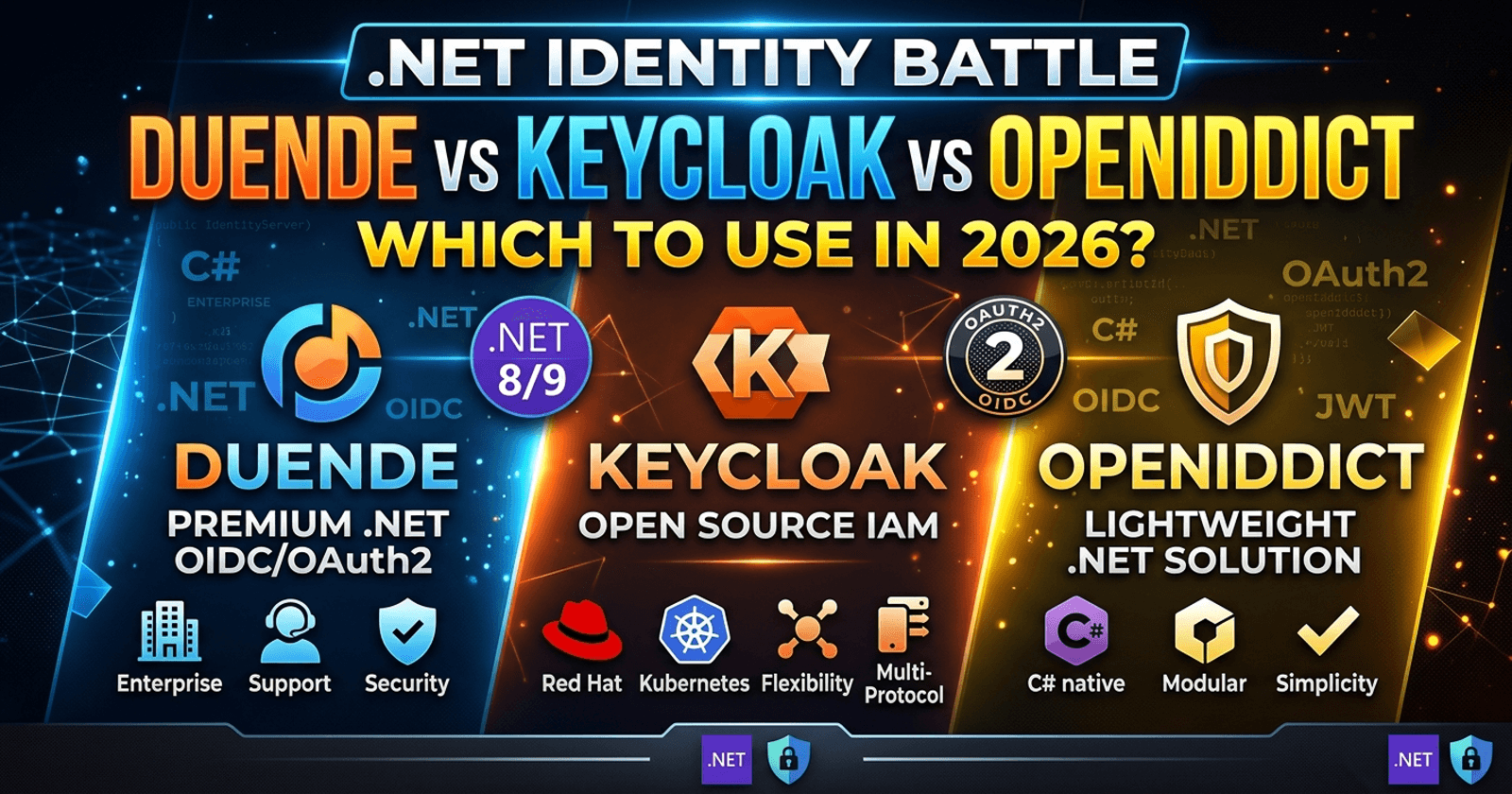
Choosing the right identity provider is one of the most consequential architecture decisions a .NET team makes. Get it wrong and you face either a runaway licensing bill, a framework that fights every custom requirement, or an operational beast that dwarfs the application it protects. In 2026, three names consistently come up when .NET teams evaluate OpenID Connect and OAuth 2.0 solutions for ASP.NET Core: Duende IdentityServer, Keycloak, and OpenIddict. Each takes a fundamentally different philosophy toward identity — and that philosophy determines whether it fits your team or frustrates it.
What Are These Three Options?
Once you have chosen your identity provider, the implementation details matter just as much as the decision. Patreon has complete, runnable source code covering the ASP.NET Core integration side — token validation, claims transformation, and the patterns your API needs to consume identity correctly.
Picking the right identity provider is the first half of the problem. The second half is knowing exactly how your ASP.NET Core API should consume the tokens it issues — JWT bearer configuration, ClockSkew, claims-based policies, and custom authorization requirements. Chapters 7 and 8 of the ASP.NET Core Web API: Zero to Production course cover the API side of that picture in full, with source code you can run immediately.
Before comparing them, it helps to understand what each option actually is — because they are not all the same kind of product.
Duende IdentityServer is a .NET library you embed into an ASP.NET Core application. You write the host, you own the UI, you supply the user store. Duende provides the OAuth 2.0 and OpenID Connect protocol machinery. It is the successor to the popular open-source IdentityServer4, rebranded and commercialised by the original authors. For commercial use beyond small startups, a paid license is required.
Keycloak is a standalone open-source identity and access management server, originally developed by Red Hat and now part of the Cloud Native Computing Foundation (CNCF). It ships as a deployable service — typically a Docker container or Kubernetes pod — with its own admin UI, user federation, social login, and MFA flows baked in. You do not embed it into your application; you integrate your ASP.NET Core app against it as an external authority.
OpenIddict is a .NET library, similar in nature to Duende IdentityServer, but fully open source under the Apache 2.0 license. It is modular, lower-level, and more "bring your own everything" than Duende. OpenIddict has no admin UI out of the box and requires you to build or wire in more pieces, but it gives you complete control without licensing constraints.
Side-by-Side Comparison
| Dimension | Duende IdentityServer | Keycloak | OpenIddict |
|---|---|---|---|
| License | Commercial (paid for production) | Apache 2.0 (free) | Apache 2.0 (free) |
| Deployment model | Embedded .NET library | Standalone server | Embedded .NET library |
| Admin UI | You build it | Built-in | You build it |
| User federation (LDAP/AD) | Manual wiring | Built-in | Manual wiring |
| Social login | Via plugins/manual | Built-in | Via plugins/manual |
| MFA | Manual wiring | Built-in | Via community add-ons |
| Learning curve | Moderate | Moderate–High | High |
| Customisation depth | Very high | Moderate | Very high |
| .NET native | Yes | No (Java) | Yes |
| Protocol standards support | Extensive | Extensive | Extensive |
| Operational footprint | Low (same process) | High (separate service) | Low (same process) |
| Community | Large .NET community | Very large CNCF community | Growing .NET community |
When Should You Use Duende IdentityServer?
Duende IdentityServer is the right call when your team needs a standards-compliant, highly customisable OIDC/OAuth server deeply integrated with the .NET ecosystem and is prepared to pay the license cost.
The sweet spot for Duende is ISV or SaaS products — companies building software for other companies, where the identity server must support complex token customisation, resource isolation, device flow, CIBA, or PAR. Duende supports all of these as first-class features, and the ASP.NET Core-native implementation means your team can apply familiar patterns for middleware, dependency injection, EF Core data stores, and custom claims transformations.
The license cost — tiered by revenue for commercial use — is significant for early-stage teams but reasonable for established software products. For teams already invested in the IdentityServer4 ecosystem, the migration path to Duende is well-documented and straightforward.
Avoid Duende when: you need built-in user federation, admin UI, or social login out of the box and do not want to build these yourself; or when budget constraints make the license a barrier.
When Should You Use Keycloak?
Keycloak is the right call when your organisation needs an enterprise-grade identity platform with batteries included — user management UI, LDAP/Active Directory federation, social login, MFA, fine-grained authorisation, and multi-realm support — and wants zero licensing cost.
The CNCF move has accelerated Keycloak's momentum. It is now a de-facto standard in Kubernetes-native enterprise environments and is widely used alongside service meshes and API gateways. If your infrastructure team already operates Keycloak for another product, adding ASP.NET Core applications as clients is low-friction.
Keycloak is also the natural choice when identity requirements include non-.NET services. Because Keycloak is a separate server, every language and framework can authenticate against it using standard OIDC discovery. This is powerful in polyglot microservices architectures.
The trade-off is operational weight. Keycloak is a Java-based service with its own database, configuration surface, and update cadence. Running it reliably in production requires dedicated operational attention — database backups, cluster sizing, upgrade testing. For small teams or applications where identity is not the core product, this overhead is material.
Avoid Keycloak when: your team is purely .NET and wants a lightweight embedded solution; when you need deep protocol customisation that Keycloak's extension model makes complex; or when the operational cost of a separate service outweighs the feature benefit.
When Should You Use OpenIddict?
OpenIddict is the right call when your team wants maximum control, zero licensing cost, and is willing to invest in building the scaffolding around the protocol core.
It is a direct fit for teams that found IdentityServer4 appealing but were pushed out by Duende's licensing — and still need a .NET-native embedded solution. OpenIddict handles the protocol layer (token issuance, validation, introspection, revocation) cleanly and correctly. It integrates tightly with ASP.NET Core's pipeline and supports EF Core and MongoDB stores. What you bring to the table: user management UI, admin tooling, social login wiring, and any non-standard flows.
OpenIddict is increasingly used in internal enterprise applications where the developer team owns both the identity server and the API surface, wants full auditability of the token pipeline, and does not need the operational weight of Keycloak or the cost of Duende.
Avoid OpenIddict when: your team does not have the capacity to build and maintain the surrounding infrastructure (admin UI, user store integration, MFA flows); or when the OIDC server must be operational within days rather than weeks.
Is There a Clear Winner?
Yes, and it depends on your context.
Choose Duende IdentityServer if you are building a commercial .NET product, need advanced protocol features, and the license cost fits your revenue stage. It is the most complete .NET-native OIDC library available.
Choose Keycloak if you need a ready-to-run identity platform with built-in user management, LDAP federation, and social login — and you can absorb the operational cost of running a separate service. It is the strongest choice for enterprise IT environments and polyglot microservices.
Choose OpenIddict if you need a free, .NET-native embedded solution and are prepared to build the surrounding tooling yourself. It is the best option for cost-conscious teams with strong .NET skills who want full control of the identity pipeline.
For teams on the fence between Duende and OpenIddict: if the license cost of Duende is not a constraint, Duende wins on completeness and community support. If the license is a barrier, OpenIddict is a serious, well-maintained alternative — not a compromise.
For teams on the fence between Keycloak and the embedded options: ask whether your team wants to own and operate a separate service. If yes, Keycloak's feature set is hard to beat. If no, pick an embedded library.
Real-World Trade-offs: A Decision Matrix
| Scenario | Recommended Choice |
|---|---|
| ISV building multi-tenant SaaS on .NET | Duende IdentityServer |
| Enterprise IT deploying across .NET and Java services | Keycloak |
| Startup needing free OIDC server embedded in .NET | OpenIddict |
| Team migrating from IdentityServer4 (already paid) | Duende IdentityServer |
| Kubernetes-native org with existing Keycloak deployment | Keycloak |
| Microservices with polyglot services | Keycloak |
| Internal enterprise app, .NET-only, full control preferred | OpenIddict |
| Small product team, tight budget, .NET stack | OpenIddict |
Anti-Patterns to Avoid
Building your own token server from scratch. Unless you are implementing JWT validation middleware on the resource side, do not roll your own OIDC server. Use one of these three.
Choosing Keycloak to "just try it" in production without operational planning. Keycloak requires a database, a sizing decision, a backup strategy, and a tested upgrade path. Deploying it as an afterthought leads to outages.
Choosing Duende without understanding the license tiers. Duende's pricing is tiered by company revenue and use case. Review it against your revenue projections before architecting around it — not after.
Using OpenIddict for a project that needs an admin UI in two weeks. OpenIddict is powerful but raw. If you need user self-service portals, admin dashboards, or MFA out of the box, plan the build time or choose a different option.
Mixing concerns by using ASP.NET Core Identity alone as an OAuth server. ASP.NET Core Identity handles user authentication within a single application. It is not an OAuth 2.0 authorization server. Use it as the user store backing one of these three solutions — not as a replacement.
For a deeper look at how ASP.NET Core handles authorization patterns, see our guide on ASP.NET Core Authorization Strategies: RBAC vs ABAC vs Policy-Based and the companion JWT Authentication vs Reference Tokens in ASP.NET Core APIs.
For the official Duende IdentityServer documentation, see docs.duendesoftware.com. For OpenIddict, the project documentation lives at documentation.openiddict.com.
☕ Prefer a one-time tip? Buy us a coffee — every bit helps keep the content coming!
FAQ
Is Duende IdentityServer free to use? Duende IdentityServer offers a free community edition for qualifying small companies and open-source projects, but commercial use above a revenue threshold requires a paid license. Review the current pricing at duendesoftware.com before committing to it for a production product.
Can I use Keycloak with ASP.NET Core? Yes. ASP.NET Core integrates with Keycloak via standard OpenID Connect middleware. You configure Keycloak as the authority in AddAuthentication().AddOpenIdConnect(...) and your application validates tokens issued by Keycloak. The integration is well-supported and widely documented.
Is OpenIddict production-ready in 2026? Yes. OpenIddict is actively maintained, follows OAuth 2.0 and OpenID Connect specifications closely, and is used in production by organisations worldwide. It is not a toy project — it is a robust framework that requires the builder to wire in supporting components like user stores and admin tooling.
What replaced IdentityServer4? Duende IdentityServer is the commercial successor, maintained by the original authors of IdentityServer4. OpenIddict is a popular open-source alternative for teams that need a free, .NET-native OIDC library. Some teams have migrated to Keycloak when they needed a fully managed identity platform.
Which identity provider is best for Kubernetes? Keycloak is the strongest choice for Kubernetes deployments. It has first-class support for containerised deployments, a Helm chart, and is part of the CNCF ecosystem. Duende and OpenIddict can also be containerised since they are embedded ASP.NET Core services, but they lack Keycloak's built-in HA clustering features.
Does OpenIddict support refresh tokens and device flow? Yes. OpenIddict supports refresh tokens, device authorization grant (device flow), client credentials, authorization code with PKCE, and other standard OAuth 2.0 and OpenID Connect flows. The feature set is comprehensive; the difference from Duende is primarily in what surrounding tooling ships out of the box.
Can I switch from Duende to OpenIddict later? Technically yes, but it requires significant work — you must rebuild the token issuance pipeline, migrate existing tokens and clients, and port any custom logic. Make the choice carefully upfront rather than treating it as easily reversible.