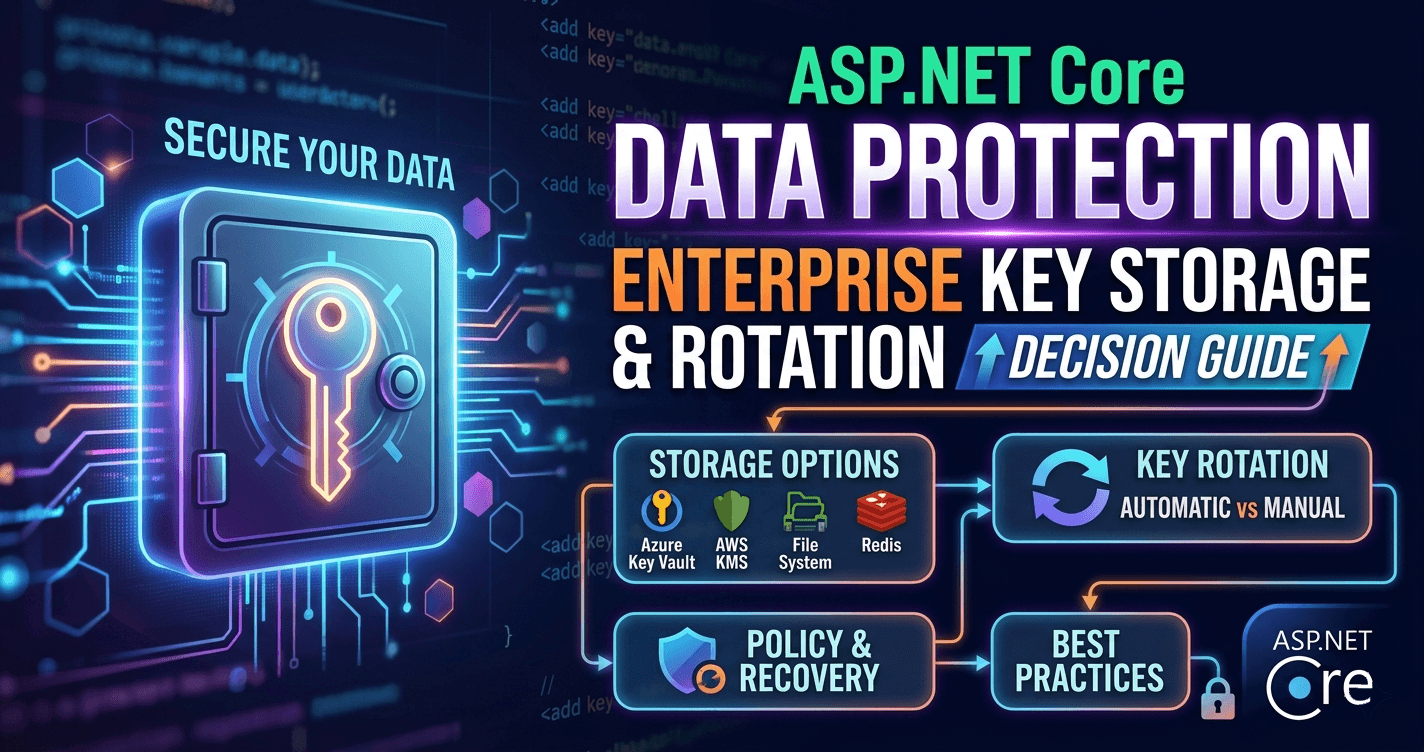
ASP.NET Core Data Protection: Enterprise Key Storage and Rotation Decision Guide
The ASP.NET Core Data Protection API is one of the most misunderstood subsystems in the entire framework. Teams reach for it when they need to protect cookies, antiforgery tokens, bearer token state, or sensitive payloads — and then discover that the default configuration silently breaks the moment they scale past a single instance. Key rings disappear on redeploy. Sessions invalidate under load balancers. Tokens become unreadable across pods. What looks like a simple encryption helper turns out to be an operational surface that demands intentional decisions at the infrastructure level.
Want implementation-ready .NET source code you can adapt fast? Join Coding Droplets on Patreon. 👉 https://www.patreon.com/CodingDroplets
This guide walks enterprise teams through the decisions that actually matter: which key storage backend to choose for your deployment model, how key rotation works and where it breaks, how purpose strings enforce isolation, and what a production-grade Data Protection configuration looks like across Kubernetes, Azure, and on-premise deployments.
What the Data Protection API Actually Does
Before any storage decision makes sense, teams need a clear mental model of what this API provides and what it does not.
The Data Protection API is a cryptographic payload protection system. It takes a plaintext payload and an application-specific purpose string, encrypts and authenticates the payload using a symmetric key derived from a managed key ring, and returns a protected byte sequence or Base64 string. The reverse operation — unprotecting — requires the same purpose string and a key ring that still contains the key used during protection.
It is not a general-purpose secrets manager. It does not replace Azure Key Vault, HashiCorp Vault, or environment variable injection for configuration values. Its scope is protecting runtime payloads — things like cookie content, CSRF tokens, password reset tokens, and temporary session state — not storing API keys or connection strings.
The framework uses Data Protection internally for cookies in authentication middleware, antiforgery tokens, and TempData. When teams use bearer tokens or OAuth, the Data Protection API often underpins the session state that validates those flows. Any misconfiguration at the key ring level ripples up into authentication failures, CSRF rejections, and opaque token validation errors that are painful to diagnose.
The Key Ring: The Core Operational Concept
Every ASP.NET Core application has a key ring — a managed set of cryptographic keys with explicit activation dates, expiry dates, and revocation states. The system automatically promotes new keys when the active key approaches expiry (default 90 days), retains old keys so previously-issued tokens remain decryptable during their validity window, and revokes keys explicitly when a breach or rotation policy requires it.
The critical enterprise insight: by default, the key ring is stored in the file system of the running process, isolated to that machine. For single-instance deployments on permanent servers, this works. For every other deployment model — Docker containers, Kubernetes pods, multi-instance web farms, Azure App Service with swap slots — the default breaks in ways that are non-obvious and hard to reproduce in local development.
When a new pod starts, it has no key ring. It generates one. Requests hitting that pod produce tokens that other pods cannot decrypt. When a pod restarts, its file-system key ring is gone. Tokens protected before the restart are unreadable after it. When App Service swap slots exchange traffic, the key ring stays with the slot, not the application. Users get unexplained authentication failures at the moment of a successful deployment.
Solving this requires selecting a shared, durable key ring storage backend that all instances can access.
Key Storage Backend Decision Guide
File System (Shared Network Path)
The file system provider works when all instances share a persistent network volume — for example, an Azure Files mount or an NFS share in Kubernetes. The setup is straightforward, but the operational model has traps. Network storage introduces latency and potential mount failures. DPAPI protection of the key ring files (Windows-only) does not survive cross-machine moves. Teams must manage file permissions explicitly.
This option suits small on-premise deployments running on Windows where shared storage already exists and managing a Redis cluster or database for key storage adds operational overhead disproportionate to the team's scale. It is not suitable for containerized workloads where persistent volume mounts add complexity and ephemeral node restarts are normal.
Azure Blob Storage
Azure Blob Storage is the cleanest option for Azure-hosted workloads. It is durable, globally redundant, and cheap for the tiny key ring payloads involved. The blob acts as a single source of truth for the key ring across all instances. Combined with Azure Key Vault for key encryption at rest, this configuration meets compliance requirements for most regulated industries.
The decision point: if the workload runs in Azure and uses Managed Identity, Blob + Key Vault is the right default. Key Vault handles encryption (using a Customer-Managed Key if required), Blob provides the storage backend, and Managed Identity eliminates the credential management problem entirely. There are no connection strings, no rotating secrets, and no additional infrastructure to run.
Teams not using Managed Identity — for example, those using client secrets or service principal certificates — need to evaluate whether adding another secret rotation concern outweighs the operational benefit.
Redis
Redis key ring storage makes sense when the workload already operates Redis as its primary cache — which is common in high-throughput ASP.NET Core deployments. The key ring lives in a Redis key, shared instantly across all instances, with automatic key expiry governed by the Data Protection API rather than Redis TTLs.
The critical constraint: Redis must have data persistence enabled (AOF or RDB). An in-memory Redis instance that restarts will lose the key ring, causing exactly the same authentication failure pattern as the file system default. Azure Cache for Redis requires the Premium tier or higher for persistence. Teams running open-source Redis on Kubernetes must configure persistence explicitly.
The secondary concern: Redis is now a security dependency, not just a performance dependency. A compromised Redis instance exposes the key ring. Network policies, TLS encryption in transit, and authentication must be hardened accordingly.
SQL Server / Entity Framework Core
The SQL Server provider (via Microsoft.AspNetCore.DataProtection.EntityFrameworkCore) stores keys in a database table. This suits teams that already operate SQL Server, want key ring management integrated into their existing backup and disaster recovery story, and prefer not to add Redis or Azure Blob Storage to their infrastructure dependency graph.
The tradeoff: database availability becomes a Data Protection dependency. If the database is unavailable during application startup — which happens during maintenance windows, failover events, or cold starts against a recovering replica — the application cannot load its key ring and will fail to start. Teams must architect database availability with this dependency in mind, which means key ring reads need to come from a highly-available replica or connection pool, not just the primary.
This option fits mature on-premise or hybrid deployments where database operations are well-understood and infrastructure teams manage SQL availability independently of application deployments.
Custom / Registry / In-Memory
The Windows registry provider suits legacy Windows deployments where file system access is restricted by IIS app pool permissions. In-memory key storage is available and exists primarily for testing; it should never appear in production configuration. Custom providers using IXmlRepository allow teams to integrate with proprietary key management systems or HSM-backed stores, but these require significant implementation investment.
Key Encryption at Rest
Storing the key ring in durable, shared storage solves the distribution problem. It does not automatically solve the protection-at-rest problem. Key ring XML is sensitive material — an attacker with read access to the storage backend can extract cryptographic keys and decrypt any payload protected with those keys.
The ASP.NET Core Data Protection API provides key encryption via IXmlEncryptor. Out of the box, it offers:
DPAPI (Windows only): Keys are encrypted using Windows Data Protection API, tied to the machine or user account. This does not translate across machines or to non-Windows deployments.
X.509 Certificate: An RSA certificate encrypts each key. The certificate itself must be protected, rotated, and distributed — which shifts the problem rather than solving it.
Azure Key Vault: This is the recommended production-grade option for Azure deployments. Each Data Protection key is encrypted using a Key Vault key (RSA-HSM or RSA). Access is governed by Key Vault access policies or RBAC. The key never leaves Key Vault; only the wrapped key material is stored. Key Vault supports Customer-Managed Keys, which satisfies data sovereignty requirements in regulated industries.
The decision rule: any deployment storing key ring material in shared storage that external systems could theoretically access — blob, SQL, Redis — should encrypt the key ring at rest using a hardware-backed option. For Azure, that means Key Vault. For on-premise, that means an HSM-backed certificate or integration with a secrets manager.
Purpose Strings and Isolation
The Data Protection API uses a purpose string — a free-form string passed to CreateProtector() — to derive a purpose-specific subkey from the key ring. Data protected under purpose A cannot be unprotected under purpose B, even if both use the same key ring. This is not access control; it is cryptographic isolation.
Enterprise teams frequently underestimate this mechanism. Common mistakes include:
Using generic purpose strings like "token" or "data" across multiple subsystems, which means a compromised token from one subsystem can potentially be replayed against another if the purpose validation logic is weak.
Failing to use purpose hierarchies — CreateProtector("Payments", "ResetToken") creates isolation between payment flows and other reset flows — when the application has multiple token issuance paths that should be cryptographically independent.
Reusing purpose strings across multiple applications sharing a key ring. If two applications share a Blob storage key ring and both use purpose "auth", a token from application A can be submitted to application B. The intended isolation requires different application discriminators: setting SetApplicationName() in the Data Protection configuration forces the system to include the application name in the key derivation.
The enterprise rule: every logical consumer of the Data Protection API — authentication cookies, password reset tokens, antiforgery state, CSRF tokens, API tokens — must use a distinct, stable purpose string. Purpose strings are part of the application's security contract. Changing them invalidates all previously issued tokens for that purpose.
Key Rotation Strategy
The Data Protection API manages key rotation automatically within its configured lifetime (default 90 days). When the active key is within KeyPropagationTime (default 2 days) of expiry, the system generates a new key and marks it as the future active key. On the expiry date, the new key becomes active and new protections use it. Old keys remain in the key ring and continue to serve unprotect operations until they are explicitly revoked.
Enterprise teams need to decide on three rotation-related questions:
Rotation frequency: The 90-day default is appropriate for most use cases. Shorter lifetimes — 30 days or less — increase the frequency of key transitions but provide a smaller blast radius if a key ring is exfiltrated. High-security environments processing payment data, health records, or government-regulated content should consider shorter lifetimes aligned with their cryptographic policy.
Emergency revocation: If a key ring is exfiltrated or suspected to be compromised, keys can be revoked explicitly. This immediately invalidates all tokens protected with the revoked key — including active sessions and tokens in circulation. Emergency revocation is a business decision, not just a technical one. Teams must have runbooks that coordinate revocation with session termination, user re-authentication flows, and customer communication.
Key propagation lag: In distributed deployments, key ring changes propagate to all instances on the next key ring read. If the read interval is long, some instances may not yet have the new active key while others have already started using it. The default propagation model handles this gracefully — new keys are added to the ring before they become active, so all instances see the new key before it starts issuing protections. Teams using aggressive caching of the key ring must account for propagation lag in their cache TTL configuration.
Multi-Tenant Considerations
Applications serving multiple tenants from a single deployment face an additional isolation requirement: tenant A's protected payloads must not be decryptable by tenant B's application logic, even if both run in the same process.
The Data Protection API supports this through purpose string hierarchies. Using CreateProtector("Tenant:{tenantId}", "ResetToken") creates per-tenant cryptographic isolation without requiring separate key rings per tenant. For most SaaS architectures, this approach is sufficient — the key ring is shared, but the derived keys are tenant-specific.
For strict data residency or compliance requirements — particularly in EU GDPR contexts where data must not cross certain borders — separate key rings per tenant, stored in region-specific backends, are necessary. This adds significant operational complexity and is only warranted when regulatory requirements explicitly mandate cryptographic isolation, not just logical isolation.
Frequently Asked Questions
What happens if the key ring is unavailable when the application starts? If the Data Protection API cannot load the key ring at startup, ASP.NET Core will throw an exception and the application will fail to start — or, in some configurations, will start with a degraded state where only new protections work and previously-issued tokens cannot be unprotected. The default behavior is a startup failure, which is safer than silently degrading. Teams should treat key ring availability as a startup health dependency and include key ring store connectivity in their health check and readiness probe configuration.
Does changing SetApplicationName break existing tokens? Yes. The application name is included in key derivation. Changing SetApplicationName() cryptographically isolates the new application from the old one — existing tokens become unreadable, existing cookies become invalid, and users will be logged out. This is the correct behavior when intentionally migrating to a new application identity, but it is a destructive operation if done inadvertently during refactoring.
Can the Data Protection API be used for encrypting database columns? Technically yes, but it is not the right tool for this use case. The Data Protection API is optimized for short-lived runtime payloads with automatic key rotation. Encrypting database columns requires long-lived keys, explicit key versioning per record, and the ability to re-encrypt records when keys rotate — none of which the Data Protection API manages. Column encryption belongs in a dedicated field-level encryption layer using stable, explicitly-managed keys, not in a system designed for session token protection.
Is Redis a valid key ring backend for a Kubernetes deployment? Yes, with the persistence caveat. If the Redis instance supports AOF or RDB persistence and is configured to retain data on restart, Redis is a reliable key ring backend for Kubernetes. A Redis deployment without persistence — including many development Redis setups — will lose the key ring on restart, causing authentication failures across the cluster. Always verify persistence is enabled before using Redis as a key ring store in production.
How should key ring storage be secured in a zero-trust environment? In a zero-trust model, the key ring store should be accessed via workload identity (Managed Identity, IRSA, or Workload Identity Federation) rather than static credentials. Network access to the store — whether Azure Blob, SQL, or Redis — should be restricted to the application's network identity via private endpoints, VPC peering, or service-to-service mTLS. The key ring itself should be encrypted at rest using a hardware-backed key (Azure Key Vault HSM, AWS CloudHSM) accessible only by the application's workload identity. Audit logging on the key store access should feed into the SOC's monitoring pipeline.
What is the difference between ASP.NET Core Data Protection and .NET's built-in AES encryption? ASP.NET Core Data Protection provides authenticated encryption — it guarantees both confidentiality (attackers cannot read the payload) and integrity/authenticity (attackers cannot modify the payload without detection). Raw AES encryption in CBC mode without a MAC is vulnerable to padding oracle and bit-flipping attacks. The Data Protection API uses AES-256-CBC plus HMACSHA256 by default, with the option to switch to AES-256-GCM via custom algorithms. For protecting tokens and cookies, always use the Data Protection API over raw AES. For general-purpose encryption of large data volumes, evaluate System.Security.Cryptography primitives directly with authenticated encryption modes.
Conclusion
The ASP.NET Core Data Protection API rewards teams that engage with its operational model directly. The defaults are safe for a single-instance deployment but silently hostile to everything else. The right production configuration — shared durable key storage, hardware-backed key encryption at rest, explicit purpose string discipline, and a rotation policy tied to your security requirements — is not complex, but it requires deliberate decisions.
Enterprise teams that treat Data Protection configuration as a deployment concern from the start — not a fix applied after the first production authentication incident — avoid an entire class of session invalidation bugs, CSRF failures, and cryptographic confusion that are particularly painful to diagnose under load.