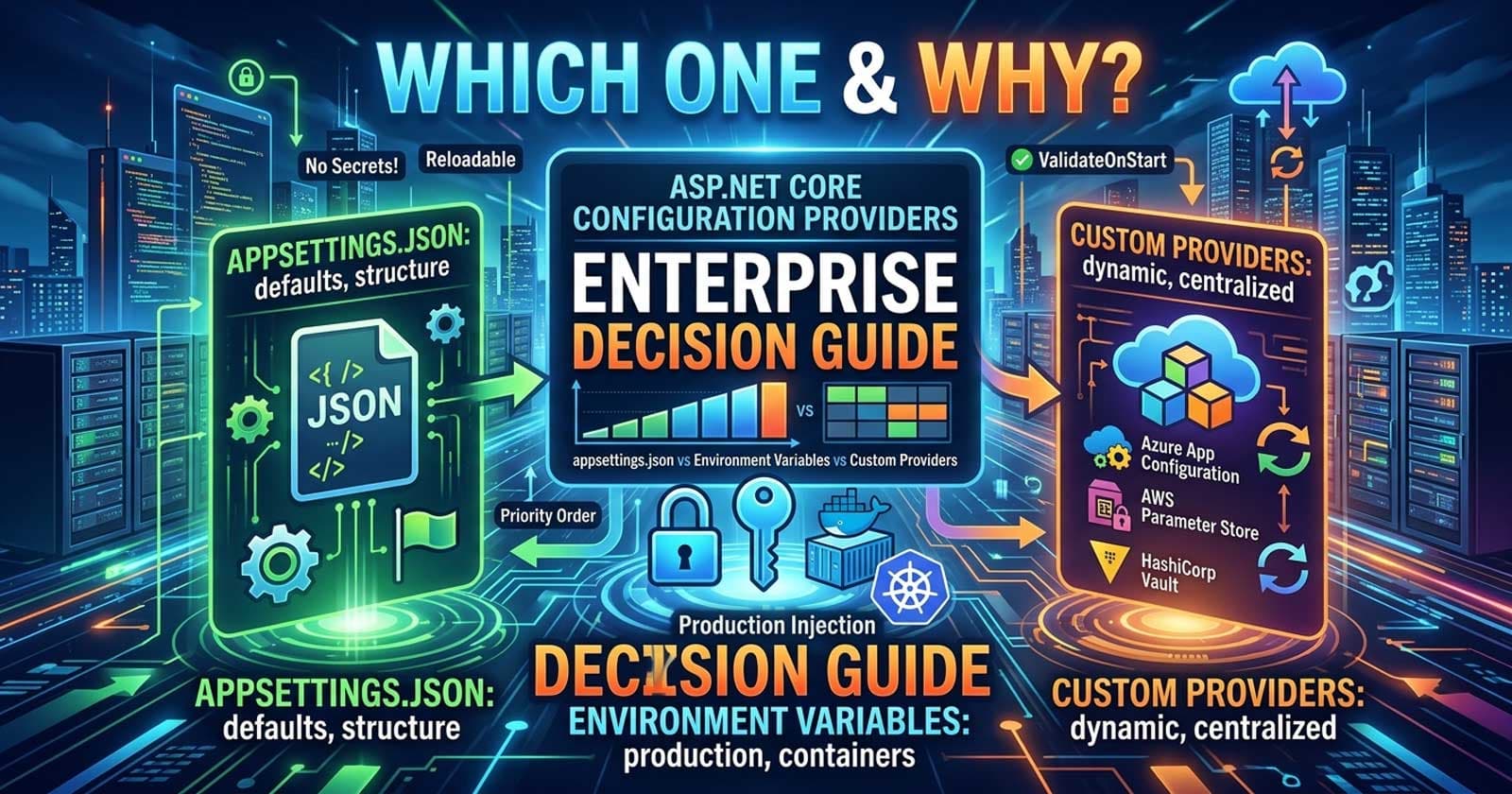
ASP.NET Core Configuration Providers in Enterprise APIs: appsettings.json vs Environment Variables vs Custom Providers — Enterprise Decision Guide
The architectural decision guide every .NET team needs before deploying to production
Managing configuration across dev, staging, and production environments is one of those problems that looks trivial until your team is three services deep and someone hardcodes a connection string into a committed JSON file. The ASP.NET Core configuration system is genuinely flexible — but that flexibility comes with real architectural decisions that matter at enterprise scale.
🎁 Want implementation-ready .NET source code you can drop straight into your project? Join Coding Droplets on Patreon for exclusive tutorials, premium code samples, and early access to new content. 👉 https://www.patreon.com/CodingDroplets
The configuration pipeline in ASP.NET Core is built on layered providers that merge into a single IConfiguration tree. Understanding which provider to reach for — and why — is the decision architects frequently get wrong, either by over-relying on appsettings.json in production or by scattering environment variables everywhere without a coherent strategy.
What Is the ASP.NET Core Configuration System?
ASP.NET Core's configuration model abstracts over a chain of IConfigurationProvider instances. Each provider reads key/value pairs from a source — a JSON file, environment variables, the command line, a database, or a vault — and merges them into a unified IConfiguration object. The last provider registered wins for any given key.
The default provider registration order (from WebApplication.CreateBuilder) is:
appsettings.jsonappsettings.{Environment}.json- User Secrets (Development environment only)
- Environment variables
- Command-line arguments
This means environment variables override appsettings.json, and command-line arguments override everything. That ordering is intentional and drives the layering strategy you should use in production.
The Three Core Approaches and When to Use Each
appsettings.json: Defaults and Non-Sensitive Structure
appsettings.json is the right home for non-sensitive structural configuration: feature flags, timeout values, pagination defaults, retry counts, and environment-agnostic service settings. It ships with the build artifact and should be committed to source control.
appsettings.{Environment}.json extends this with per-environment overrides. Use appsettings.Production.json for production-specific non-sensitive values like logging levels or request size limits. Do not use it for connection strings, API keys, or credentials — those belong in a higher-priority, non-committed source.
When appsettings.json is the right choice:
- Structural settings that belong in code review (feature flags, timeouts, pagination config)
- Default values that are safe to commit
- Logging configuration per environment
- Non-sensitive feature switches
When appsettings.json is the wrong choice:
- Any credential, secret, or API key
- Values that differ between deployment instances (not just environments)
- Anything that needs to change without redeployment
Environment Variables: The Production Injection Layer
Environment variables are the standard production configuration channel for containerised and cloud-native workloads. They override appsettings.json at runtime, are not committed to source control, and are well-supported by Kubernetes ConfigMaps and Secrets, Docker Compose, Azure App Service Application Settings, and AWS Elastic Beanstalk.
ASP.NET Core maps nested configuration keys to environment variables using double underscores (__) as the section separator. Database__ConnectionString binds to the Database:ConnectionString key in IConfiguration.
When environment variables are the right choice:
- Containerised workloads (Docker, Kubernetes)
- Cloud-hosted deployments (Azure App Service, AWS ECS, GCP Cloud Run)
- Connection strings and URLs that differ per deployment environment
- Values controlled by your platform team rather than your dev team
When environment variables are the wrong choice:
- Large structured configuration objects (environment variables are flat key/value, not hierarchical)
- Credentials requiring rotation without restart (environment variables are read at startup)
- Teams that need a configuration audit trail or approval workflow
Custom Configuration Providers: When You Need More
Custom configuration providers extend IConfigurationSource and IConfigurationProvider. They load configuration from any source: a database table, an internal HTTP service, HashiCorp Vault, AWS Parameter Store, or Azure App Configuration.
ASP.NET Core ships with several production-grade providers beyond JSON and environment variables:
| Provider | Package | Use Case |
|---|---|---|
| Azure App Configuration | Microsoft.Azure.AppConfiguration.AspNetCore |
Centralised config with feature flags, dynamic reload |
| AWS Systems Manager | Amazon.Extensions.NETCore.Setup |
Parameter Store integration |
| HashiCorp Vault | VaultSharp |
Secret injection with lease rotation |
| Database (custom) | DIY | Tenant-specific or user-configurable settings |
Azure App Configuration with feature flags is particularly strong for enterprise SaaS where different tenants may have different feature states.
When custom providers are the right choice:
- Multi-tenant SaaS with per-tenant configuration
- Dynamic configuration that must reload without a restart
- Secrets requiring automatic rotation (HashiCorp Vault, Azure Key Vault with references)
- Centralised config management across multiple services
- Audit-trail requirements on configuration changes
How Do Configuration Providers Work at Runtime?
Provider Priority and Merge Semantics
The configuration system performs a last-registered-wins merge. If appsettings.json sets "Timeout": 30 and an environment variable sets Timeout=60, the value at runtime is 60. If Azure App Configuration sets Timeout=45 and is registered after environment variables, it wins.
Understanding this merge order is critical when debugging unexpected configuration values in production. A common production issue is a stale cached value from appsettings.Production.json overriding a runtime environment variable — usually because the wrong registration order was used.
Configuration Validation at Startup
One of the most under-used features in the ASP.NET Core configuration system is startup validation. The Options Pattern supports ValidateDataAnnotations() and ValidateOnStart(), which fail fast at startup rather than at the first usage of a misconfigured value.
This is especially important in production where a missing or malformed connection string should crash the application at startup, not during the first database call from a live user request.
Without startup validation, misconfiguration manifests as runtime exceptions, often far from the root cause in your logs.
Is Dynamic Configuration Reload Safe?
reloadOnChange: true on JSON providers and IOptionsSnapshot<T> / IOptionsMonitor<T> enable live configuration updates without restarting the host. The distinction matters:
IOptions<T>— singleton, never reloads. Safe for immutable settings, can mask stale config.IOptionsSnapshot<T>— scoped, reloads per request. Correct for settings that must be fresh per HTTP call.IOptionsMonitor<T>— singleton with reload callbacks. Correct for background services and settings that change over the lifetime of the application.
In enterprise workloads, using IOptionsSnapshot<T> for settings that only change on deployment and IOptionsMonitor<T> for truly dynamic configuration (feature flags, rate limits) is the correct division.
The Enterprise Decision Matrix
| Scenario | Recommended Approach |
|---|---|
| Local dev environment | appsettings.Development.json + User Secrets |
| Docker / Kubernetes deployment | Environment variables + Kubernetes Secrets |
| Azure-hosted SaaS | Azure App Configuration + Key Vault references |
| AWS-hosted services | AWS Systems Manager Parameter Store |
| Multi-tenant per-tenant config | Custom database-backed provider |
| Feature flags with runtime toggle | Azure App Configuration feature management |
| Shared config across 10+ services | Centralised config service (App Config / Consul) |
| Static structural settings | appsettings.json committed to source control |
| CI/CD pipeline overrides | Command-line arguments or environment variables |
Common Anti-Patterns in Production Configuration
Anti-Pattern 1: Secrets in appsettings.json
The most common configuration mistake is storing connection strings, API keys, or third-party credentials directly in appsettings.json or appsettings.Production.json. These files end up in the repository, in Docker images, and in build artefacts — all of which can be exfiltrated. The correct pattern is appsettings.json for structure, environment variables or vault for secrets.
Anti-Pattern 2: Flat Environment Variables for Deep Configuration
Environment variables are flat key/value pairs. Using them for complex nested configuration produces unwieldy names (Endpoints__Api__Upstream__BaseUrl__TimeoutSeconds=30), errors that are hard to debug, and no type safety. Deep or structured configuration belongs in appsettings.json with a shallow environment-variable override for the sensitive leaf values.
Anti-Pattern 3: No Startup Validation
Relying on configuration values being present at the first usage site rather than validating at startup means misconfiguration causes runtime failures in production, often silently — or only when a specific code path is hit. Use ValidateOnStart() with the Options Pattern.
Anti-Pattern 4: Over-Reloading in High-Throughput APIs
Enabling reloadOnChange: true on JSON providers in high-throughput APIs creates filesystem watcher threads and can cause GC pressure. In Kubernetes, ConfigMap reloads are already handled by the platform. Use IOptionsMonitor<T> only where dynamic reload is genuinely needed, not as a default.
Anti-Pattern 5: Mixing Configuration Concerns
Storing both feature flags and database credentials in the same configuration file or provider conflates concerns with different security and lifecycle requirements. Structural settings, operational settings, and secrets should be managed through separate providers with appropriate access controls.
What Should Your Enterprise Configuration Strategy Look Like?
A well-structured enterprise configuration strategy for ASP.NET Core in 2026 generally follows this layering:
- Base layer —
appsettings.json: Committed, structural, non-sensitive defaults - Environment layer —
appsettings.{Environment}.json: Per-environment structural overrides, also committed - Secret layer — Environment variables or vault references: Connection strings, API keys, credentials — never committed
- Dynamic layer (optional) — Azure App Configuration / Consul: Feature flags, tenant overrides, operational toggles that change without redeployment
- Validation layer — Options Pattern with
ValidateOnStart(): Fail fast at startup if required values are missing or malformed
Each layer has a clear owner. Developers own layers 1 and 2. Platform or DevOps teams own layer 3. Product or release teams own layer 4.
☕ Prefer a one-time tip? Buy us a coffee — every bit helps keep the content coming!
What Is the Best Configuration Strategy for ASP.NET Core in Production?
The best strategy is layered: appsettings.json for structural defaults, environment variables for deployment-time secrets and overrides, and a centralised config service (Azure App Configuration, AWS Parameter Store, or Consul) if you need dynamic reload or cross-service consistency. Validate all required settings at startup using ValidateOnStart(). Never store credentials in JSON files.
Frequently Asked Questions
What is the priority order of configuration providers in ASP.NET Core?
The default order is: appsettings.json → appsettings.{Environment}.json → User Secrets (Development only) → Environment variables → Command-line arguments. Later-registered providers override earlier ones for the same key. You can change this order by customising your ConfigurationBuilder in Program.cs.
Should I use IOptions, IOptionsSnapshot, or IOptionsMonitor in my ASP.NET Core service?
Use IOptions<T> for settings that never change after startup (connection strings, fixed service URLs). Use IOptionsSnapshot<T> in scoped services where the value needs to reflect the latest configuration on each request. Use IOptionsMonitor<T> in singleton services or background workers that need to react to configuration changes at runtime without restarting.
How do I validate configuration at startup in ASP.NET Core?
Use the Options Pattern with ValidateDataAnnotations() and ValidateOnStart() in Program.cs. This causes the application to throw an exception on startup if any required configuration values are missing or fail their validation constraints, rather than failing silently at runtime.
Is it safe to enable reloadOnChange on appsettings.json in Kubernetes?
Generally not recommended for high-throughput services. Kubernetes already manages ConfigMap updates through pod environment or volume mounts. Enabling reloadOnChange: true on JSON files inside a container adds filesystem watcher overhead without benefit, since the file doesn't change inside a running container. Use IOptionsMonitor<T> backed by Azure App Configuration or a similar provider if you need live reload.
What is the correct way to store connection strings in ASP.NET Core production?
Connection strings should never be committed to source control. In local development, use User Secrets (dotnet user-secrets). In production, inject them as environment variables (set via your deployment platform — Kubernetes Secrets, Azure App Service Application Settings, AWS Secrets Manager) or reference them from a vault (Azure Key Vault, HashiCorp Vault) using a dedicated configuration provider.
When should I build a custom configuration provider?
Build a custom configuration provider when your application needs configuration from a source not covered by built-in providers — such as a database table, a multi-tenant configuration service, or an internal HTTP API. A common enterprise use case is per-tenant configuration in SaaS applications, where each tenant has different feature limits or integration endpoints that need to be loaded from a shared configuration store at startup and refreshed periodically.
How does Azure App Configuration differ from appsettings.json?
Azure App Configuration is a managed service that centralises configuration across multiple services, supports dynamic reload via change events, integrates with Key Vault references for secrets, and provides a built-in feature flag management interface. appsettings.json is a local file that ships with your build artefact, has no dynamic reload capability at the platform level, and has no access control beyond file permissions. For enterprise multi-service workloads, Azure App Configuration solves the cross-service consistency and dynamic reload problems that appsettings.json cannot.
For more .NET architecture content, explore Coding Droplets or browse related articles on ASP.NET Core Options Pattern, secrets management, and enterprise API design.