ASP.NET Core Security in 2026: 11 Production Mistakes Developers Still Make (and How to Fix Them)
If you’re building APIs in ASP.NET Core, security mistakes usually don’t come from “not knowing security.” They come from shipping fast, copy-pasting old patterns, and skipping boring guardrails.
As of early 2026, with .NET 10 projects gaining traction and AI-assisted coding speeding up delivery, the gap between feature velocity and security hygiene is getting wider. This guide gives you practical fixes for the most common production mistakes.
Why this matters now
Attack surfaces are wider (mobile, SPA, public APIs, third-party webhooks)
Teams are shipping more frequently
Misconfiguration issues still cause the majority of preventable incidents
If you fix the 11 items below, you dramatically reduce real-world risk.
1) Returning raw exceptions to clients
Mistake: Returning stack traces/internal exception messages in API responses.
Fix: Use centralized exception handling middleware and return safe error contracts.
Related video from Coding Droplets:
2) Weak JWT token implementation
Mistake: Long-lived access tokens, poor signing key management, no revocation strategy.
Fix:
Short-lived access tokens
Proper refresh token rotation
Store refresh tokens securely and revoke on suspicious activity
Related video:
3) No API versioning strategy
Mistake: Breaking old clients after endpoint changes.
Fix: Use explicit versioning (URL/header/media type) from day one, and document each version in OpenAPI/Swagger.
Related video:
4) Insecure deployment without proper TLS/SSL
Mistake: Delayed SSL setup or manual certificate renewals that silently fail.
Fix: Enforce HTTPS, automate certificate renewal, and monitor expiry alerts.
Related video:
5) Misusing HTTP semantics (especially GET bodies)
Mistake: Sending request bodies with GET and assuming all clients/proxies will behave.
Fix: Keep GET idempotent and body-free. Use query params for filters, POST for complex payloads.
6) Skipping model validation and input normalization
Mistake: Trusting incoming DTOs blindly.
Fix:
Enforce server-side validation
Normalize inputs (trim, canonicalize)
Reject invalid payloads early with clear 400 responses
7) Over-permissive CORS configuration
Mistake: AllowAnyOrigin + AllowCredentials patterns and broad wildcard setups.
Fix: Restrict by exact origin, method, and headers per environment.
8) Over-fetching sensitive data
Mistake: Returning full entities when clients only need a subset.
Fix: Use response DTOs and minimize payloads (performance + security win).
9) Missing authZ checks at the business layer
Mistake: Assuming [Authorize] at controller level is enough.
Fix: Add resource-level authorization checks in services/handlers as a second safety layer.
10) No rate limiting / abuse protection
Mistake: Public endpoints with unlimited request rates.
Fix: Configure ASP.NET Core rate limiting policies by route/user/IP and add anomaly monitoring.
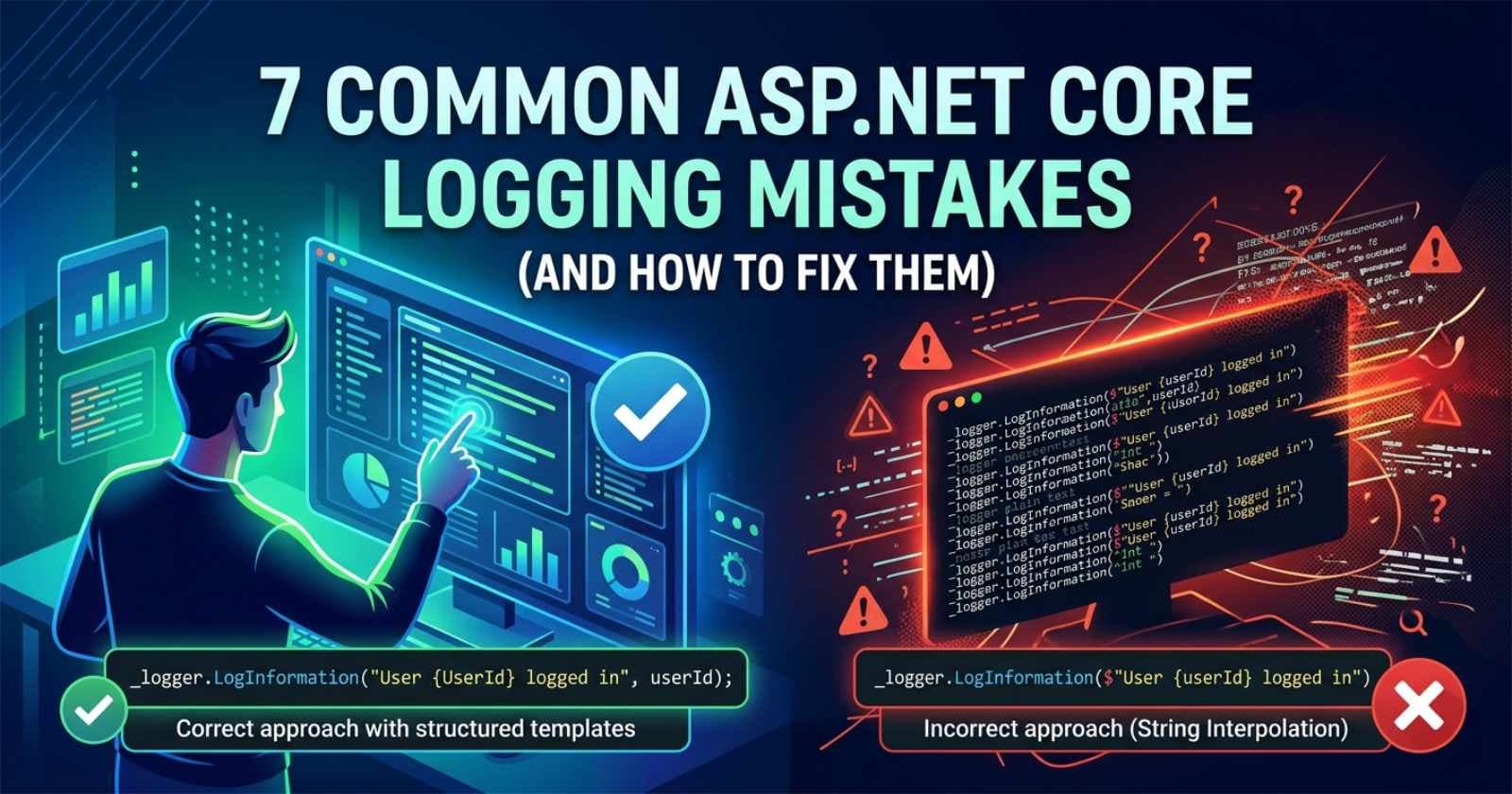
11) Poor observability for security events
Mistake: Logs exist, but no actionable security telemetry.
Fix:
Structured logs (correlation IDs)
Alerting on auth failures and token anomalies
Audit trails for high-risk operations
Final thoughts
Most API security failures are not advanced cryptography failures. They are architecture and process failures. Fixing these 11 issues gives you a strong baseline for secure, scalable ASP.NET Core APIs in 2026.
If you’re actively building in .NET, Coding Droplets has practical videos that map directly to these topics and can help you implement each fix quickly.