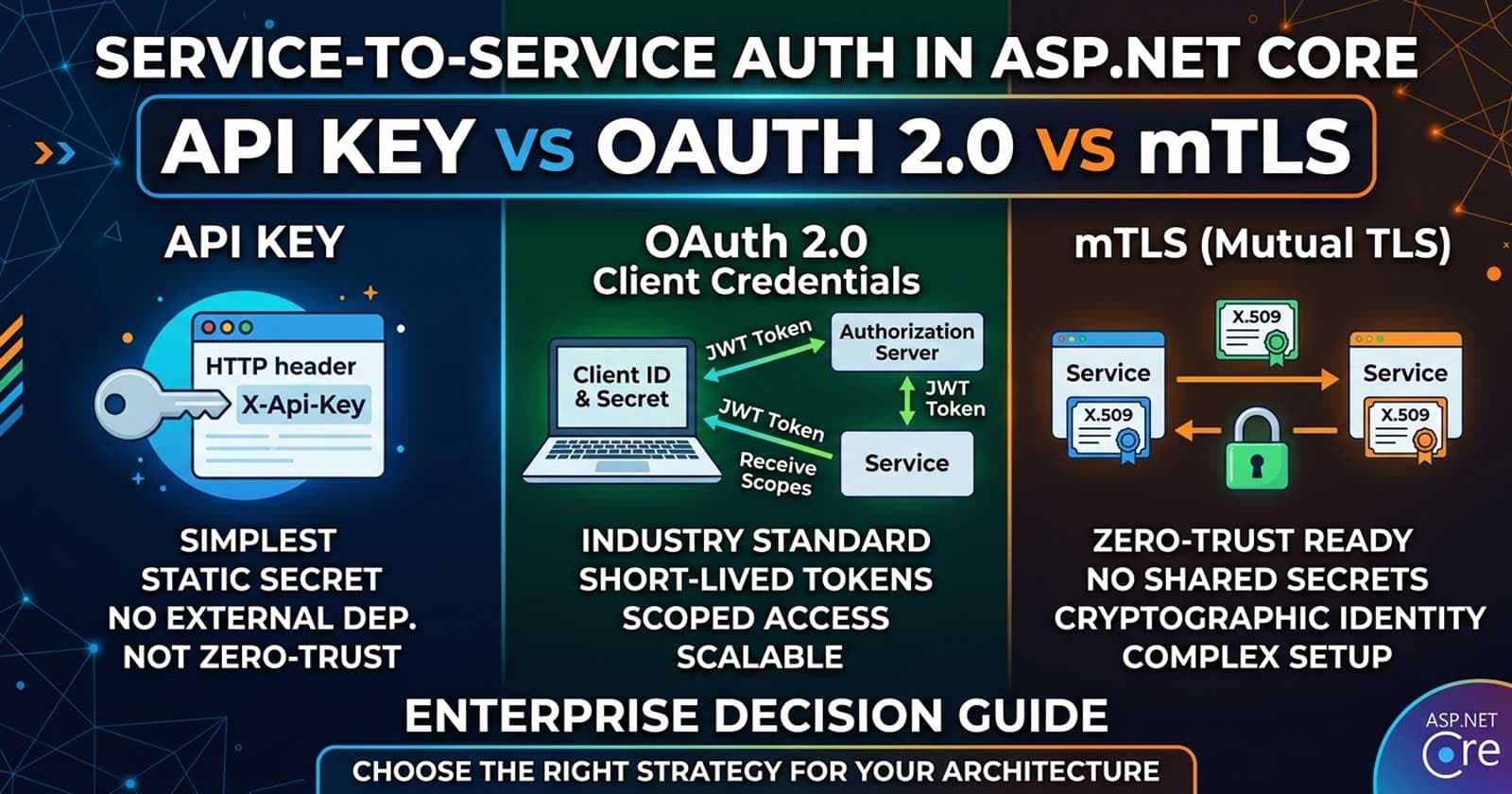
Service-to-Service Authentication in ASP.NET Core: API Key vs OAuth 2.0 Client Credentials vs mTLS — Enterprise Decision Guide
When two services in your system need to talk to each other — an API calling a billing service, a background job invoking a notification endpoint, or a data pipeline reading from an internal catalog — the question that immediately surfaces is: who vouches for that caller, and how?
Service-to-service authentication in ASP.NET Core is a different problem from user authentication. There's no browser, no interactive login, and no human to present credentials. The authenticating identity is a machine, and the strategy you choose will govern your security posture, operational overhead, and how well your internal APIs hold up under a zero-trust model. If you want to go deeper on the full implementation — including production-ready ASP.NET Core projects that wire authentication, policies, and API key middleware together — Patreon has annotated source code that covers precisely these integration points.
Understanding how each mechanism maps to real enterprise constraints matters most before you write a single line of code. Chapter 8 of the Zero to Production course walks through API key middleware for M2M scenarios alongside role-based and policy-based authorization — all inside the same running API so the context never gets lost.
Why Service-to-Service Auth Deserves Its Own Decision
User authentication solves a fundamentally different problem. A human provides credentials interactively; tokens expire and get refreshed by the browser. In a service mesh or microservice architecture, however, a payment service calls an invoice service hundreds of times per minute, automatically, with no human intervention. The properties that matter change:
- Revocation speed — how fast can you cut off a compromised identity?
- Rotation burden — how often and how painlessly can you rotate credentials?
- Auditability — can you trace a specific service identity in your logs?
- Zero-trust readiness — does your approach hold if an attacker reaches the internal network?
Each of the three main patterns answers these questions differently.
The Three Contenders
API Key Authentication
An API key is a shared secret: a long, random string the calling service includes in a header (typically X-Api-Key) or as a query parameter. The receiving service validates it against a registry — usually a database lookup or a cached hash comparison.
What it does well:
- Trivial to implement and audit. Every HTTP log that captures request headers automatically captures the key identity.
- No external dependency at call time. Validation is local or a fast cache hit.
- Works in any HTTP client without token-handling libraries.
Where it falls short:
- A leaked key is permanently valid until manually rotated. There is no automatic expiry.
- It is a knowledge factor only — anyone who intercepts the network request has the key.
- At scale, a large matrix of service-to-service keys becomes a rotation and governance nightmare.
- No standardized metadata beyond the key itself — you can't embed scopes, expiry, or issuer claims in the token natively.
When it fits enterprise use: API keys are a pragmatic fit for internal services behind a private network where traffic never crosses the public internet, particularly when the team count is small, rotation discipline is high, and the acceptable risk of a compromised credential is low. They are not zero-trust-ready. If someone reaches your internal network, every key-protected endpoint is effectively open.
OAuth 2.0 Client Credentials Flow
The Client Credentials grant is the standard OAuth pattern for M2M authentication. Each service is registered as a client in an authorization server (Duende IdentityServer, Keycloak, Auth0, Azure AD, or a custom OAuth 2.0 implementation). At call time, the calling service exchanges its client_id and client_secret for a short-lived JWT access token, then presents that token to the receiving service as a Bearer token in the Authorization header.
What it does well:
- Tokens are short-lived (typically 5–60 minutes). A compromised token expires quickly without manual intervention.
- Tokens carry auditable claims:
client_id,scope,aud(audience),exp,iat. Your logs know which service made a request and what it was authorized to do. - Scope-gating is built in. The invoice service can require
scope:invoices.readand reject any caller that lacks it — without custom middleware. - Standard format means any off-the-shelf JWT validation middleware (
AddJwtBearer) handles validation without custom code. - Token rotation is automatic. The calling service requests a new token before expiry using standard OAuth library helpers.
Where it falls short:
- Requires an authorization server — either self-hosted or cloud-managed. That's an operational dependency that must be highly available.
- Token issuance adds latency. A cold cache means a round-trip to the auth server before the first real call.
- Client secrets are still a knowledge factor. If the secret leaks, an attacker can impersonate the service until the secret is rotated.
When it fits enterprise use: Client Credentials is the right default for most enterprise teams. It balances security (short-lived tokens, scopes, standard validation) against operational cost (one centralized auth server, standard libraries). The pattern scales naturally from two services to two hundred. It is also an industry standard — security teams, auditors, and new engineers immediately understand what they're looking at.
Mutual TLS (mTLS)
mTLS goes beyond what you know (a secret) to what you have (a certificate). Both the client and server present X.509 certificates during the TLS handshake. The server verifies the client's certificate is signed by a trusted certificate authority (CA), and the client likewise validates the server's certificate. Identity is proven cryptographically at the transport layer — before a single byte of HTTP payload is sent.
What it does well:
- True zero-trust security. Even if an attacker is inside your network, they cannot impersonate a service without a certificate signed by your internal CA.
- No shared secrets. There is nothing to leak at the application layer — the private key never leaves the service that owns it.
- Certificate revocation (CRL/OCSP) allows fast invalidation. Short-lived certificates further reduce the blast radius of compromise.
- ASP.NET Core 10 supports certificate authentication natively. Kestrel can be configured to require and validate client certificates, and
AddCertificateAuthentication()maps certificate subject names to identity claims.
Where it falls short:
- Certificate issuance, rotation, and distribution is complex without automation. Manual certificate management at scale is worse than managing API keys.
- Requires a PKI — an internal CA, certificate lifecycle tooling (SPIFFE/SPIRE, cert-manager on Kubernetes, Vault PKI), and service teams that understand certificate rotation.
- Not all infrastructure passes TLS client certificates cleanly. Load balancers, API gateways, and proxies may terminate TLS and strip the client cert before it reaches ASP.NET Core — requiring careful configuration or pass-through mode.
- Debugging TLS failures is harder than debugging a missing header or an expired token.
When it fits enterprise use: mTLS is the right choice when you have a regulatory mandate (financial services, healthcare, government) for cryptographic proof of service identity, or when your threat model explicitly includes lateral movement inside your own network. Most teams reach for mTLS at a later stage of maturity, often in conjunction with a service mesh (Istio, Linkerd) that handles certificate lifecycle automatically.
Side-by-Side Comparison
| Dimension | API Key | OAuth 2.0 Client Credentials | mTLS |
|---|---|---|---|
| Implementation complexity | Very low | Medium | High |
| Token/credential lifetime | Manual rotation only | 5–60 minutes | Certificate lifetime (hours to days if automated) |
| Zero-trust ready | No | Partial | Yes |
| External dependency | None | Auth server required | PKI / CA required |
| Scope-based authorization | Custom only | Built-in (OAuth scopes) | Via claims in cert or external policy |
| Audit trail | Key ID in header | Client ID + scope in token | Certificate subject in log |
| Rotation automation | Manual | Supported by OAuth libraries | Requires PKI tooling (cert-manager, SPIFFE) |
| Standard tooling support | Yes | Yes | Requires TLS config awareness |
| Recommended for | Minimal-overhead internal services | Default enterprise M2M auth | Regulated environments or zero-trust mandates |
How Does This Map to Your ASP.NET Core Architecture?
Is your service exposed beyond a private network?
If yes — even to a VPN or partner network — rule out plain API keys without additional controls. A stolen key on a semi-public route is a persistent breach.
Do you have a compliance requirement for cryptographic identity?
PCI DSS, FedRAMP, and HIPAA-adjacent architectures frequently require that service identities are verified by certificate. If that is your context, design for mTLS from the start and invest in certificate lifecycle tooling before shipping production traffic.
Do you already operate an authorization server?
If your organization already runs Keycloak, Duende IdentityServer, or Azure Active Directory for user authentication, adding Client Credentials for M2M costs almost nothing operationally. The infrastructure is already there.
How mature is your platform team?
API keys require disciplined rotation culture. mTLS requires platform-level certificate automation. Client Credentials requires auth server availability SLAs. Honest assessment of team maturity matters — an overly complex choice that is misconfigured in production is worse than a simpler choice done correctly.
Anti-Patterns to Avoid
Sharing tokens between services. Each service-to-service relationship should use a distinct credential — whether that is a unique API key, a dedicated OAuth client, or a service-specific certificate. Shared credentials mean a single compromise cascades across multiple service boundaries.
Long-lived Client Credentials tokens cached in application state. Standard OAuth library implementations handle token refresh automatically and transparently. Avoid building your own caching layer unless you fully understand token expiry semantics and have test coverage for the refresh path.
Using API keys in query string parameters. Query strings appear in server logs, CDN access logs, browser history, and proxy traces. Always put authentication credentials in headers, never in URLs.
Treating internal network trust as a security boundary. Network perimeters fail. An attacker with access to one internal service should not automatically have access to all others. Service-to-service authentication enforces identity at the application layer regardless of network position.
Mixing Client Credentials and user tokens without explicit audience separation. A user token and a service token must validate against different audiences. Your [Authorize] policy on internal service endpoints should explicitly require the client_credentials grant type or a specific aud value that no user token satisfies.
Making the Decision
For most ASP.NET Core teams in 2026, OAuth 2.0 Client Credentials is the correct default. It offers automatic expiry, scoped authorization, standard validation middleware, and a clear audit trail — without the infrastructure overhead of a full PKI. The investment in an authorization server pays for itself quickly as service count grows.
Use API keys when: you have two or three internal services behind a hard private network boundary, you need to ship quickly, and you have a rotation policy backed by your secrets management tooling (Azure Key Vault, HashiCorp Vault, or similar).
Adopt mTLS when: you have a compliance mandate, you are operating a service mesh that handles certificate lifecycle for you, or your threat model requires cryptographic identity proof at the transport layer.
Whatever mechanism you choose, the principle is the same: every service must prove its identity before being granted access to another service's resources, and that proof should be auditable, rotatable, and resilient to credential compromise.
☕ Prefer a one-time tip? Buy us a coffee — every bit helps keep the content coming!
Frequently Asked Questions
What is the simplest way to implement service-to-service authentication in ASP.NET Core?
The simplest approach is API key authentication via a custom middleware that reads the X-Api-Key header and validates it against a stored hash. ASP.NET Core does not include built-in API key middleware, but it is straightforward to write using IMiddleware or as an authentication handler implementing AuthenticationHandler<ApiKeyAuthenticationOptions>. For most enterprise scenarios, OAuth 2.0 Client Credentials offers comparable simplicity with significantly better security properties through short-lived tokens.
Can ASP.NET Core validate OAuth 2.0 Client Credentials tokens without writing custom code?
Yes. AddJwtBearer() in Microsoft.AspNetCore.Authentication.JwtBearer validates Client Credentials-issued JWTs using standard claims (aud, exp, iss, scope). Once you configure the authority URL, audience, and required scopes, the middleware handles validation automatically. No custom token parsing is needed.
Is mTLS practical for teams without a dedicated platform or DevOps function?
Generally, no — not without automation tooling. Managing certificate issuance, rotation, and distribution manually across more than a handful of services is error-prone and operationally intensive. Teams without platform support should start with Client Credentials and plan an mTLS migration once certificate lifecycle automation (cert-manager on Kubernetes, Vault PKI, or SPIFFE/SPIRE) is in place.
How does service-to-service auth interact with the ASP.NET Core authorization pipeline?
Service-to-service auth works through the same authentication and authorization middleware pipeline as user auth. You register a second authentication scheme (AddJwtBearer("ServiceScheme") or a custom handler) and use [Authorize(AuthenticationSchemes = "ServiceScheme")] on controllers or endpoints that should only accept machine callers. Policies can further require specific claims (client_id, scope) to ensure the correct service is calling.
What happens if the authorization server is unavailable during Client Credentials token validation?
Token validation is offline once the JWT signing keys are cached. ASP.NET Core's AddJwtBearer() fetches the signing keys from the authorization server's JWKS endpoint and caches them locally. Validation continues without contacting the auth server for the lifetime of the cached keys — typically 24 hours unless the cache is explicitly cleared. New token issuance requires the auth server to be available, which is why high availability for your auth server is critical.
Should internal microservices use the same identity provider as the one handling user authentication?
They can, and often do. Using a single authorization server for both user and service identities simplifies operations and gives you a unified audit log. The key is maintaining clear separation: user tokens use the Authorization Code flow and carry user identity claims; service tokens use the Client Credentials flow and carry client_id and scope claims. Policies on your internal endpoints should explicitly enforce which token type is acceptable.
What is the recommended approach for secret storage when using OAuth 2.0 Client Credentials?
The client_secret should never be hardcoded or stored in source control. In production, load it from a secrets management system: Azure Key Vault via AddAzureKeyVault(), HashiCorp Vault via the Vault C# client, or environment variable injection from a CI/CD secrets store. The .NET Options pattern with IOptions<ServiceCredentialOptions> provides a clean way to inject the secret into the token acquisition service without scattering configuration reads throughout the codebase. For a full walkthrough of this hierarchy in a production API, see the ASP.NET Core Web API: Zero to Production course.