Preventing Mass Assignment Vulnerabilities in ASP.NET Core APIs: An Enterprise Security Guide
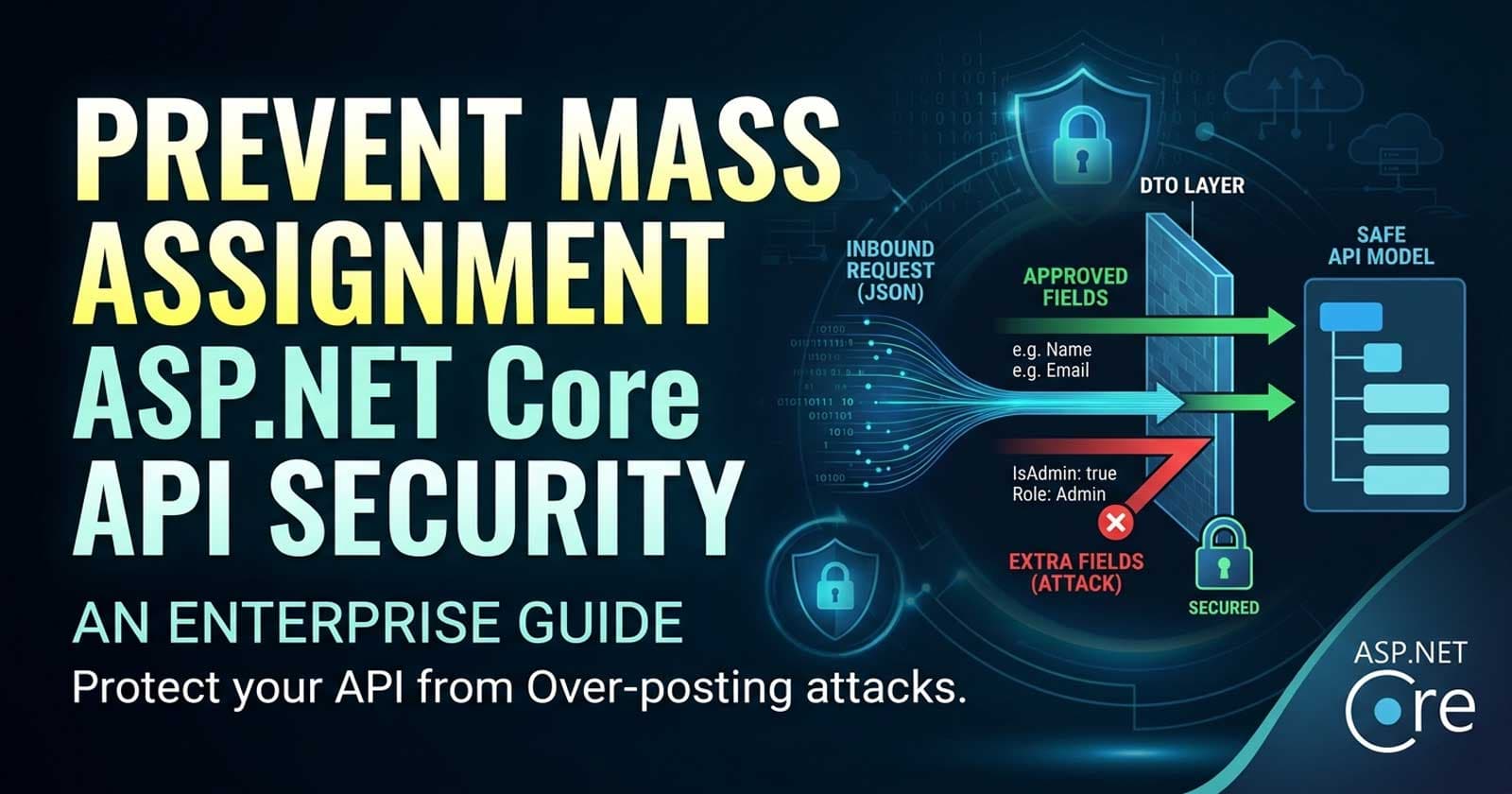
Mass assignment — also known as over-posting — is one of those vulnerabilities that looks harmless in a code review but causes significant damage in production. An attacker crafts an HTTP request with extra fields your API was never supposed to accept, and your model binder happily maps them to properties that control billing tiers, admin flags, or account roles. No exploit code required. No SQL injection. Just a JSON key that should not have been accepted. If your production APIs bind request bodies directly to domain entities or EF Core models, this guide is for you.
The full production-hardened implementation — including layered DTO patterns, property whitelisting, FluentValidation integration, and a complete test suite that validates the binding boundary — is available on Patreon, alongside the annotated source code enterprise teams actually ship.
What Is a Mass Assignment Vulnerability?
Mass assignment occurs when an API endpoint automatically binds inbound request data to an object's properties without restricting which properties are settable. In ASP.NET Core, the default model binder maps every JSON key in the request body to a matching property on the bound type. If your bound type is your EF Core entity — or any type that exposes properties like IsAdmin, AccountTier, CreditBalance, or Role — an attacker can set those values by simply including the key in their request.
The vulnerability is not a framework bug. It is an architectural decision that ignores the trust boundary between client input and server state. The framework does exactly what you told it to do. The mistake is in what you bound the request to.
This is documented as part of OWASP API Security Top 10 — API6: Mass Assignment, where it sits alongside Broken Object Level Authorization and Excessive Data Exposure as one of the most commonly exploited API vulnerabilities in modern applications.
Why It Stays Hidden Until It Matters
Mass assignment is particularly insidious in enterprise teams because:
It is almost never caught in code review — the binding looks clean and intentional
It produces no errors, no warnings, and no logs at the time it fires
It exploits the same trusted path as legitimate requests — no anomaly detection fires
Its impact is proportional to what properties the bound type exposes, which grows over time as features are added
A class that was safe to bind a year ago may have grown an IsAdmin property through a refactor last sprint. Nobody updated the endpoint. The vulnerability appears silently with the next deployment.
The Vulnerable Pattern
The most common form looks like this: a controller action accepts the entity type directly from [FromBody], and the model binder sets every matching field from the request.
Consider an endpoint that allows a user to update their profile. The request model is the User entity, which also carries IsAdmin, AccountTier, and PlanId properties that were never meant to be user-controlled. The binding happens automatically. There is no guard. If an attacker sends a request body containing "IsAdmin": true, the model binder sets it. If SaveChangesAsync() is called without filtering, the change persists.
The same pattern appears in product update endpoints, order creation flows, and anything that binds [FromBody] to an EF Core entity or a shared DTO that doubles as both an API contract and a domain model.
What ASP.NET Core Gives You by Default
ASP.NET Core provides two built-in mechanisms that partially address the problem, but neither is sufficient on its own.
[BindNever] decorates a property to exclude it from model binding entirely. It is accurate and explicit, but it requires developers to annotate every sensitive property on every class that participates in binding — and it couples your domain model to a presentation-layer attribute. When the domain model is shared across layers, that coupling creates its own maintenance burden.
[BindRequired] and [Bind("PropertyA,PropertyB")] on the action method allow you to whitelist which properties are bound from the query string and form data. This approach is explicit but fragile: the allowlist must be updated in sync with every model change, and nothing in the compiler warns you when they drift.
Both attributes signal intent, but neither enforces a systematic boundary.
The Right Approach: Dedicated Input DTOs
The production-grade solution is to introduce a dedicated input DTO — a plain class whose only purpose is to represent the data a client is allowed to send for a given operation. The DTO exposes only the properties that users should control. The mapping from DTO to entity happens in your service or command handler, where you explicitly assign the values you want.
This pattern means the attack surface of your endpoint is defined by the DTO's property list, not by the entity's property list. If the entity gains a new field, the DTO is unaffected. The binding boundary is explicit, intentional, and survives refactoring.
For a UpdateProfileRequest DTO, the only properties are DisplayName, Bio, and AvatarUrl. The controller binds to this type. Inside the service, you read from the DTO and write only those three fields to the User entity. IsAdmin, AccountTier, and everything else is never touched, regardless of what the request contained.
This is not additional complexity — it is the standard layered architecture pattern that Clean Architecture, CQRS with MediatR, and most enterprise ASP.NET Core codebases already use. The DTO is both the security boundary and the API contract.
How Does This Differ From Validation?
Validation and binding protection solve different problems. FluentValidation or Data Annotation validators fire after the model binder has already populated the object. They check whether the values are acceptable — not whether the fields were supposed to be bound at all. If IsAdmin is bound to true before validation runs, a validator that checks DisplayName.Length will not help you.
The two layers are complementary:
Binding boundary (DTO): Controls which fields are accepted from the request
Validation (FluentValidation): Controls whether the accepted values are valid
Rely on one without the other and you have a gap. A narrow DTO with no validation accepts any string for DisplayName. A broad entity with thorough validation still accepts IsAdmin if it is on the bound type.
Protecting Bulk and Nested Operations
The problem scales with complexity. Bulk create/update endpoints, nested resources, and operations that accept arrays of objects all multiply the attack surface unless each nested type is also a dedicated input DTO.
A common mistake is correctly protecting a top-level resource but accepting nested objects that are entity types. If your CreateOrderRequest is a clean DTO but OrderItem binds directly to the OrderItem entity — which has a UnitCostOverride property — the vulnerability is still reachable through the nested type.
Every type that participates in request binding, at every depth, needs to be a purpose-built input type. Shared types that appear on both the read path and write path are a red flag.
Detecting Exposure Before Attackers Do
Teams that want to audit existing endpoints for exposure can use a systematic approach:
Identify every controller action that accepts
[FromBody]Inspect the bound type — is it an entity, a shared DTO, or a dedicated input model?
For each bound type, list every public settable property
Identify which of those properties should never be client-controlled
If any such properties exist, the endpoint is potentially vulnerable
This audit takes less than a day on most codebases and frequently surfaces assumptions baked in years ago that nobody has reviewed since.
Automated tooling can help: a custom Roslyn analyzer can flag any controller action where the [FromBody] parameter type has properties decorated with [DatabaseGenerated], [Key], or lives in a namespace associated with your data layer. This is a heuristic, not a guarantee, but it catches the common patterns at compile time.
Defence-in-Depth Checklist
A single DTO layer is necessary but not sufficient for enterprise APIs. A layered approach covers the gaps:
DTO-first binding — every
[FromBody]parameter is a dedicated input DTO, never an entityExplicit property mapping — services map from DTOs to entities; never use AutoMapper with untrusted input types unless projection profiles are explicitly restricted
Read/write model separation — the type used for read responses is never the same type used for write requests
Audit logging on sensitive writes — log which user changed which field, not just that a change occurred
Authorization before data application — verify the caller has the right to perform the operation and the right to set the values they are submitting
Dependency review cadence — review bound types quarterly; any entity that has grown new properties may need endpoint-level review
Integration tests that assert binding boundaries — test that submitting an unsupported field in the request body has no effect on the stored entity
The last point is frequently skipped. An integration test that sends "IsAdmin": true in the body of a profile update request and then asserts the user is not an admin in the database is the only automated guard that catches an accidental DTO regression.
Is AutoMapper Safe to Use Here?
AutoMapper is a popular choice for reducing boilerplate in DTO-to-entity mapping. Used correctly, it is safe — but it introduces its own risk if misconfigured.
CreateMap<UpdateProfileRequest, User>() maps only the properties the DTO exposes, which is safe. But if a developer adds a convenience mapping like CreateMap<User, User>() or enables .ReverseMap() on a mapping that involves an entity, the safety guarantee breaks down.
The rule is: AutoMapper profiles that involve entity types on the destination side should be audited carefully. Use explicit ForMember configurations to exclude any destination properties that must not be set from external input. Where in doubt, prefer manual mapping for write operations — it is explicit, readable, and easy to audit.
Real-World Impact
Mass assignment vulnerabilities have caused significant production incidents across the industry. The 2012 GitHub incident — where a researcher escalated his own privileges to organization owner via an over-posting attack on a Rails application — is the canonical example. The same class of vulnerability has appeared in financial platforms where users set their own account tiers, e-commerce systems where customers set their own prices, and SaaS products where users promoted themselves to admin.
These are not theoretical edge cases. They are the consequence of the default behaviour of model binding combined with the natural drift of production codebases over time.
Where Should This Enforcement Live?
A question teams frequently debate: should binding protection be enforced at the controller layer, the service layer, or both?
The answer is both, with different responsibilities:
Controller layer: Accept only dedicated input DTOs via
[FromBody]— this is the binding boundaryService/command handler layer: Explicitly map from the DTO to the entity — this is the application of values
The service layer must not accept the raw input DTO as its "model" either. Commands in a CQRS pattern should be constructed from validated DTO values, not passed through wholesale. This way, if the controller binding layer is ever bypassed (internal service calls, background job triggers), the service layer still only applies what it explicitly maps.
☕ Prefer a one-time tip? Buy us a coffee — every bit helps keep the content coming!
FAQ
What is mass assignment in ASP.NET Core?
Mass assignment in ASP.NET Core occurs when a controller action binds an HTTP request body directly to a type that exposes properties the client should not be able to set — such as IsAdmin, Role, or AccountTier. The model binder populates all matching properties automatically, which means an attacker can set sensitive server-side state by including extra fields in their request body.
What is over-posting and how is it different from mass assignment?
Over-posting and mass assignment describe the same attack from slightly different angles. Over-posting refers to the act of sending more fields than the API expects. Mass assignment refers to the effect — those extra fields being automatically assigned to the target object. In ASP.NET Core, both terms describe the same vulnerability arising from unguarded model binding.
How do I prevent mass assignment in ASP.NET Core Web API?
The most reliable approach is to use dedicated input DTOs for every [FromBody] parameter. A DTO exposes only the properties the client is allowed to set. Inside your service or command handler, you explicitly map from the DTO to the entity, touching only the fields you intend to update. This eliminates the attack surface by construction rather than relying on opt-out annotations.
Does [BindNever] fully protect against mass assignment?
[BindNever] protects individual properties when applied correctly, but it is fragile as a primary defence. It requires every sensitive property to be explicitly annotated, which creates a maintenance burden as models evolve. A missed annotation on a new property re-opens the vulnerability. Use [BindNever] as a supplementary guard, not as the primary boundary.
Is AutoMapper safe to use with input DTOs in ASP.NET Core?
AutoMapper is safe when configured correctly. A mapping from a dedicated input DTO to an entity only maps the DTO's properties, which is the intended behaviour. The risk arises when entity-to-entity mappings, .ReverseMap() on write paths, or overly permissive mapping profiles are used. Audit AutoMapper profiles that have entity types as destinations to confirm no unintended properties can be set from external input.
How does mass assignment relate to OWASP API Security Top 10?
OWASP lists mass assignment as API6 in the API Security Top 10. It describes the vulnerability as occurring when an API automatically binds client-provided data to an internal object without filtering which properties can be updated. OWASP recommends explicit allowlisting of writable properties — which dedicated input DTOs achieve by design.
Can integration tests catch mass assignment vulnerabilities?
Yes, and they are the most reliable automated guard. Write integration tests that send unsupported or attacker-controlled fields in the request body — such as "IsAdmin": true in a profile update request — and then assert that the stored entity state was not affected. If the test passes (the entity is unchanged), your binding boundary is holding. If it fails, you have a regression that a reviewer likely missed.
Should the service layer also enforce binding restrictions?
Yes. The controller's DTO boundary is the outer gate, but the service layer should also apply only the values it explicitly maps from the command or DTO it receives. Services that accept raw DTO objects and persist them wholesale bypass the architectural intent. Use explicit property assignment or a strictly scoped AutoMapper profile at the service boundary, especially for write operations.