What's New in ASP.NET Core 10 Authentication & Authorization: Key Upgrades Every .NET Team Should Know in 2026
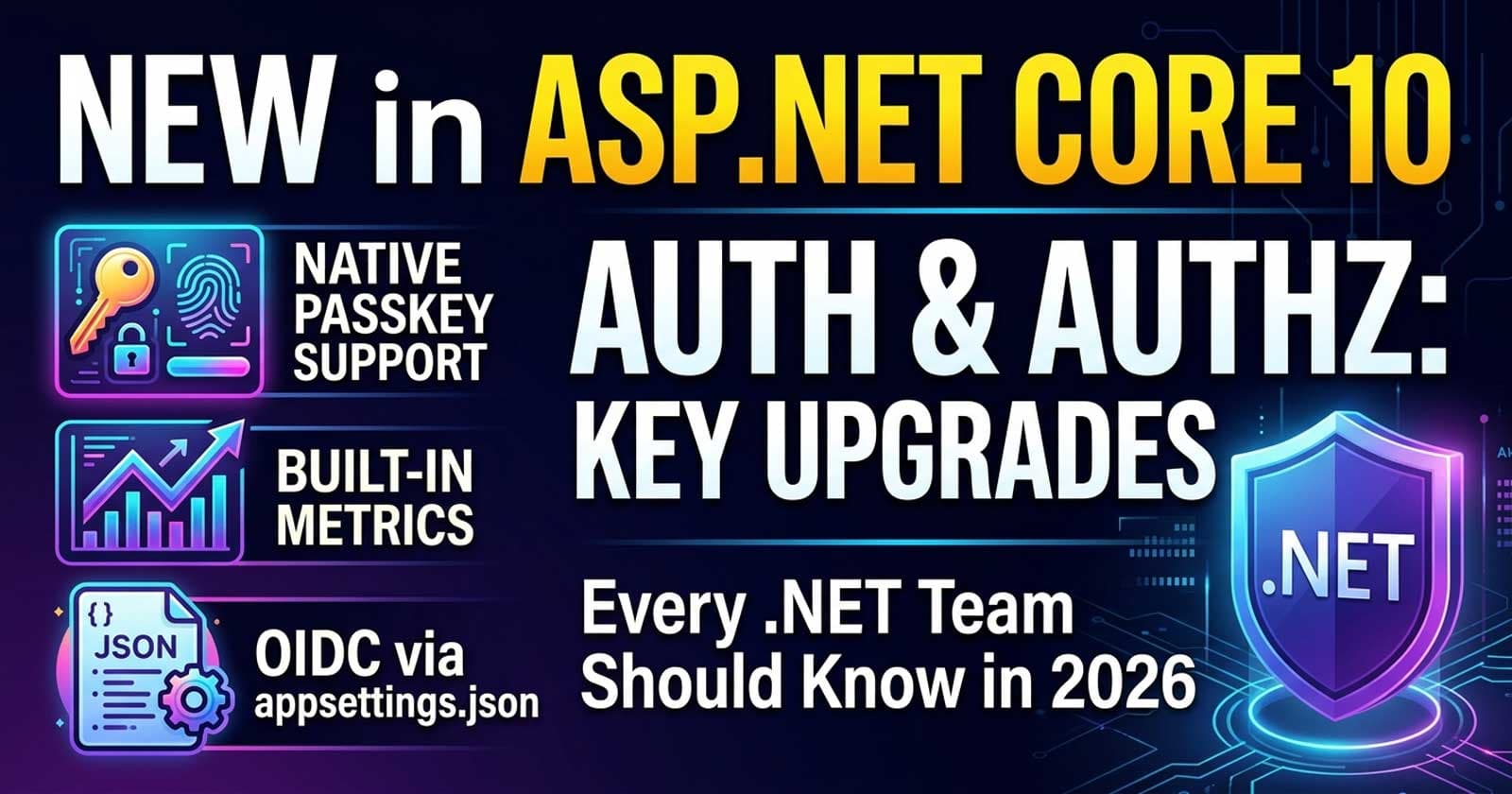
ASP.NET Core 10 authentication and authorization received some of the most developer-facing improvements in recent memory. If your team ships APIs or web applications on the .NET stack, the changes in this release — from built-in passkey support and new observability metrics, to OIDC refinements and cleaner claims handling via C# 14 — are worth understanding before your next production deployment.
The patterns covered here go deeper on Patreon — with annotated, production-ready source code that maps directly to what enterprise teams actually ship.
Understanding how these changes fit into the bigger picture of securing a full ASP.NET Core API — alongside JWT, refresh tokens, and policy-based authorization — is exactly what Chapter 7 and Chapter 8 of the Zero to Production course cover. Both chapters walk through auth inside a full production codebase, so the context is always clear.
What Changed in .NET 10 Authentication and Authorization
The authentication and authorization stack in ASP.NET Core 10 addresses three distinct problem categories: phishing-resistant credentials, developer-experience friction with claims, and observability gaps. Each is addressed by a specific set of changes, and they compound well for teams already investing in modern .NET infrastructure.
Passkey Support Is Now Built Into ASP.NET Core Identity
Passkeys — the FIDO2/WebAuthn standard for passwordless, phishing-resistant authentication — are no longer a third-party integration concern. ASP.NET Core Identity in .NET 10 ships with native support for passkey registration and authentication. The implementation uses the IdentityPasskeyOptions class to configure the Relying Party ID, authenticator timeout, and challenge size.
This is not a general-purpose WebAuthn library. The scope is deliberately narrow: it covers the most common authentication scenarios and integrates seamlessly with the existing Identity pipeline. Template support lands in the Blazor Web App template first, with API-only integration requiring manual wiring.
What enterprise teams should know before adopting:
- Attestation is not validated by default, which means you cannot cryptographically verify the authenticity of the authenticator device at registration. For high-assurance environments, additional attestation tooling is required.
- Passkeys are treated as a primary factor, not a second factor for MFA flows. Teams currently layering passkeys onto a 2FA pipeline should test this distinction explicitly.
- The feature is opinionated about how identity stores are structured — custom
UserStoreimplementations may require adaptation.
For organizations already using ASP.NET Core Identity for employee-facing or customer-facing applications, this removes the dependency on libraries like Fido2NetLib for the common case. For teams requiring full WebAuthn spec compliance, a dedicated FIDO2 library remains the better fit.
Authentication and Authorization Metrics Are Now Built In
.NET 10 introduces first-class metrics for authentication and authorization events via the System.Diagnostics.Metrics API. These metrics emit counters for authentication challenges, successful authentication, failed authentication, authorization successes, and authorization failures — all exposed through the standard metrics pipeline.
The practical impact is significant. Previously, teams instrumenting auth events had to build custom middleware, parse ASP.NET Core logs, or rely on APM vendor-specific integrations to answer basic questions like: how many requests per minute are failing authentication? How often is a specific policy denying access? What percentage of requests are triggering an authorization challenge?
All of that now comes for free and flows directly into OpenTelemetry-compatible exporters, Prometheus, and Azure Monitor without additional instrumentation code.
Where does this matter in practice?
For APIs with multiple authentication schemes (JWT bearer + API key + cookie), per-scheme metric breakdowns let teams identify misconfiguration in production before users report it. A spike in aspnetcore.authentication.challenge events on a specific scheme is a signal worth routing to your alerting pipeline.
For multi-tenant SaaS applications, tracking authorization failure rates per tenant or per policy is now a zero-infrastructure-cost operation with .NET 10's built-in metrics.
These metrics integrate directly with the OpenTelemetry setup covered in Chapter 14 of the Zero to Production course. If your team has already configured the OpenTelemetry SDK for traces and spans, auth metrics slot in automatically.
OIDC Configuration Can Now Be Loaded From appsettings.json
A persistent friction point for teams using ASP.NET Core's built-in OpenID Connect middleware has been the requirement to configure OIDC in code, making secrets management and environment-specific overrides awkward to maintain.
.NET 10 adds a JSON configuration provider path for OIDC and Microsoft Entra ID setups. The authority, client ID, scopes, and callback paths can all be configured through appsettings.json with the same environment-override mechanics as the rest of the ASP.NET Core configuration system.
This is particularly useful for teams running in Kubernetes, where environment-specific configuration injection via ConfigMap or Secret objects is the standard pattern. The new configuration path makes OIDC a first-class citizen of the ASP.NET Core configuration hierarchy rather than a special case.
Entra ID configurations also gain two new guidance areas in .NET 10: an encrypted distributed token cache for web farm scenarios, and support for Azure Key Vault with Managed Identities for data protection key storage. Both address common production headaches when scaling out ASP.NET Core applications behind a load balancer.
C# 14 Extension Members Clean Up Claims Handling
One of the most practically useful changes for teams writing .NET 10 APIs is not directly a framework feature — it is a C# 14 language feature that transforms how teams interact with ClaimsPrincipal.
The traditional approach to reading claims from the current user principal in a controller or service is built around LINQ queries over User.Claims with string-typed ClaimTypes constants. This pattern is brittle, repetitive, and provides no compile-time safety for the claim type strings.
C# 14 introduces extension members — an evolution of extension methods that allows defining computed properties and methods on existing types from within a static class. The language feature ships with .NET 10 and enables teams to write clean, testable, IntelliSense-discoverable claims accessor extensions for ClaimsPrincipal.
A properly structured ClaimsPrincipalExtensions class with extension properties for UserId, Email, and TenantId eliminates the magic strings from controllers entirely, centralizes claim parsing logic, and makes the resulting code self-documenting. The properties surface in IntelliSense just like native members, which matters when multiple developers are working in the same codebase.
Why Does This Matter for Enterprise APIs?
In multi-tenant APIs, claim access is happening on every authenticated request. Centralizing that logic in typed extension members means one place to update when claim schemas change, one place to add validation, and one place to test. The reduction in scattered Claims.FirstOrDefault(...) calls across controllers and services is meaningful at any code base size above a few dozen files.
Cookie Authentication Behavior Changes for API Endpoints
In .NET 10, the behavior of cookie authentication on API endpoints has been refined. Previously, an API endpoint protected with cookie authentication would return a 302 Found redirect to the login page when an unauthenticated request arrived — the standard browser-facing behavior. This is incorrect for API consumers, which expect a 401 Unauthorized response.
.NET 10 introduces improved handling that detects the context of the request and returns semantically correct responses for API scenarios. Teams that have been working around this with custom OnRedirectToLogin event handlers can simplify that code in .NET 10.
This change also makes ASP.NET Core APIs more consistent with RFC 7235 and the Problem Details RFC 7807 standard, which aligns with the broader trend of ASP.NET Core defaulting to machine-readable error responses over browser-optimized redirects.
Coding Droplets has covered the full Problem Details and error handling strategy in API Response Standardization in ASP.NET Core — the cookie auth fix in .NET 10 complements that guidance directly.
What Enterprise Teams Should Adopt Now vs Later
Not every change in the .NET 10 auth stack demands immediate adoption. Here is a practical adoption guide:
Adopt now:
- Built-in auth metrics — zero migration cost, directly into existing observability pipelines. Enable OpenTelemetry metric export if not already active.
- OIDC configuration via appsettings.json — simplifies environment management and Kubernetes config injection immediately.
- C# 14 extension members for claims — a refactor that pays dividends on the first pull request.
Adopt carefully:
- Passkeys in ASP.NET Core Identity — validate the attestation limitation against your security posture. For consumer-facing apps, native passkeys are ready. For high-assurance identity (government, finance, healthcare), understand the attestation gap before deploying.
Watch but defer:
- Cookie auth behavior changes — test existing cookie-auth API flows explicitly before upgrading to confirm behavior is as expected in your setup.
Migration Impact for Teams on .NET 8 and .NET 9
The auth and authz changes in .NET 10 are almost entirely additive. No breaking changes affect the core IAuthenticationService, IAuthorizationService, or the ClaimsPrincipal type. The passkey support is opt-in. The metrics are emitted automatically but require no code changes in existing setups.
The C# 14 extension members feature requires targeting .NET 10 (or C# 14 explicitly) — it is not available as a backport. Teams migrating from .NET 8 or .NET 9 should plan this as part of the SDK upgrade rather than a separate step.
The OIDC configuration path from appsettings.json is new but does not invalidate existing code-based OIDC configuration. Both approaches continue to work in .NET 10.
Do Not Miss These Supporting Features
Beyond the headline changes, two smaller improvements are worth bookmarking:
Improved Claims Transformation API — the IClaimsTransformation pipeline receives improvements that make it easier to augment claims from external sources (databases, external identity providers) with better caching semantics and async-safe patterns.
Authorization Middleware Short-Circuit Improvements — the authorization pipeline in .NET 10 handles short-circuiting more consistently when used alongside endpoint routing and fallback policies. Teams with complex policy hierarchies in multi-tenant APIs should test this explicitly during upgrade.
☕ Prefer a one-time tip? Buy us a coffee — every bit helps keep the content coming!
FAQ
Is passkey authentication in ASP.NET Core 10 production-ready?
For most consumer and enterprise application scenarios, yes. The built-in passkey support in ASP.NET Core Identity covers the common WebAuthn registration and authentication flows and integrates with the existing Identity pipeline. However, attestation is not validated by default, which means cryptographic verification of the authenticator device is not included out of the box. Teams with high-assurance security requirements should evaluate whether the built-in implementation meets their compliance standards before deploying.
How do I enable the new authentication and authorization metrics in .NET 10?
The metrics are emitted automatically when your application runs on .NET 10 — no configuration is required to start collecting them. To export them to your observability backend, configure the OpenTelemetry Metrics SDK with the AddAspNetCoreInstrumentation() builder method, which picks up authentication and authorization metrics alongside the standard HTTP pipeline metrics. If you are already exporting OpenTelemetry metrics, the auth metrics appear automatically after upgrading to .NET 10.
Can I configure OIDC from appsettings.json without changing existing code-based configuration?
Yes. The JSON configuration provider path for OIDC in .NET 10 is additive. Existing code-based configuration continues to work unchanged. The new appsettings.json path is an alternative that provides environment-specific override capability through the standard ASP.NET Core configuration hierarchy. Teams migrating incrementally can move individual OIDC settings to appsettings.json over time without breaking anything.
What is the difference between the C# 14 extension members feature and extension methods?
Extension methods, available since C# 3, allow you to add methods to existing types. C# 14 extension members extend this to include properties and other member types — computed properties, indexers, and static members — defined on existing types from a static class. For ClaimsPrincipal, this means you can define a UserId property that reads and parses the correct claim, and access it as User.UserId in controllers rather than through a method call. The result is more natural, property-style access with full IntelliSense support.
Does the cookie authentication fix in .NET 10 require any code changes?
If your existing code uses a custom OnRedirectToLogin event handler specifically to return 401 instead of 302 for API consumers, that custom code can likely be removed after upgrading to .NET 10. The framework now detects API endpoint context and returns semantically correct responses automatically. However, test your existing flows explicitly before removing the custom handlers — behavior depends on how the endpoint is configured and which authentication schemes are involved.
Are there any breaking changes in the .NET 10 authentication stack?
No breaking changes affect the core authentication and authorization APIs. The IAuthenticationService, IAuthorizationService, ClaimsPrincipal, and the major middleware types remain stable. All new features are opt-in or additive. Teams upgrading from .NET 8 or .NET 9 should test passkey configuration and cookie auth behavior explicitly on API endpoints, but the framework does not remove or modify any existing public APIs in the auth stack.
Does the passkey feature in .NET 10 support multi-factor authentication?
Not currently. In .NET 10, passkeys in ASP.NET Core Identity are treated as a primary authentication factor, not a second factor for MFA flows. This means passkeys replace passwords as the primary credential rather than augmenting them as an additional verification step. Teams requiring FIDO2 as a second factor alongside a password should evaluate third-party WebAuthn libraries until the Identity system adds MFA passkey support in a future release.